How to Protect Android Apps Against Godfather Malware
This Knowledge Base article describes how to use Appdome’s AI/ML in your CI/CD pipeline to continuously deliver plugins that Protect Godfather Malware in Android apps.
What is Godfather Malware?
Godfather is an Android banking Trojan that targets over 500 banking and cryptocurrency apps across 16 countries globally. It uses overlay attacks to mimic legitimate app interfaces, tricking users into entering login credentials on fake screens. By exploiting Android’s Accessibility Services, Godfather monitors user interactions and intercepts SMS messages, enabling it to bypass two-factor authentication (2FA) mechanisms. The malware’s ability to masquerade as trusted financial applications and dynamically evade detection makes it a significant threat. Developers and security professionals should protect against Godfather malware to prevent financial losses, unauthorized access, and data breaches, which carry severe risks for both users and businesses. Godfather’s specific capabilities include monitoring Accessibility Services to capture interactions, performing overlay attacks to harvest login credentials, intercepting SMS for 2FA bypass, and using deceptive tactics to gain permissions and access sensitive data without raising suspicion. Godfather can also mimic user actions on infected Android devices with new gesture automation commands.
How does Appdome Protect Android Apps Against Godfather Malware?
Taking all the above into consideration, you can use Appdome to protect against Godfather using a combination of the following protection methods:
- RASP & App Shielding – Prevents Godfather from injecting itself into installed apps and repackaging them. Also includes anti-tampering, anti-debugging, anti-emulator, and other protections against dynamic attacks at runtime.
- Code Obfuscation – Protects against decompiling and malicious reverse engineering which hackers use to read and understand source code.
- Root Detection – Protects mobile apps from running on rooted devices, which exposes apps to tampering, data theft, and malware by giving attackers elevated access to system files and app data.
- MitM Attack Prevention – Prevents Godfather from intercepting or hijacking sessions to harvest or steal data that it uses to conduct ATOs.
- Overlay Attack Prevention – Detects and prevents fake/malicious screen overlays from displaying on top of the app screen and concealing the legitimate app screen.
- Keylogging Prevention – Prevents the use of malicious keyloggers which are used to intercept two-factor authentication codes or harvest sensitive information.
- Accessibility Services Malware Defense – Prevents malicious actions taken by malware that exploit Android’s AccessibilityService, which is abused by Godfather to intercept sensitive inputs like passwords and 2FA codes, OTPs, take screenshots, and simulate user actions such as taps and swipes.
- Google Play Store Signature Validation – Protects against fake apps, clones, masquerading.
Each of the protections above is linked to the relevant knowledge base article for that feature, which provides detailed information about each feature and explains how to implement the protection in your Android app.
Prerequisites for Using Appdome's Protect Android Apps Against Godfather Malware Plugins:
To use Appdome’s mobile app security build system to Protect Godfather Malware , you’ll need:
Appdome account (create a free Appdome account here)
A license for Protect Against Godfather Malware
Mobile App (.apk or .aab for Android)
Signing Credentials (see Signing Secure Android apps and Signing Secure iOS apps)
How to Implement Protect Godfather Malware in Android Apps Using Appdome
On Appdome, follow these simple steps to create self-defending Android Apps that Protect Godfather Malware without an SDK or gateway:
-
Designate the Mobile App to be protected.
-
Upload an app via the Appdome Mobile Defense platform GUI or via Appdome’s DEV-API or CI/CD Plugins.
-
Android Formats: .apk or .aab
-
Protect Android Apps Against Godfather Malware is compatible with: Java, JS, C++, C#, Kotlin, Flutter, React Native, Unity, Xamarin, Cordova and other Android apps.
-
-
Select the defense: Protect Android Apps Against Godfather Malware.
-
-
Follow the steps in Sections 2.2-2.2.2 of this article to add the Protect Android Apps Against Godfather Malware feature to your Fusion Set via the Appdome Console.
-
When you enable Detect Bank Trojan Apps you'll notice that the Fusion Set you created in step 2.1 now bears the icon of the protection category that contains Protect Android Apps Against Godfather Malware.
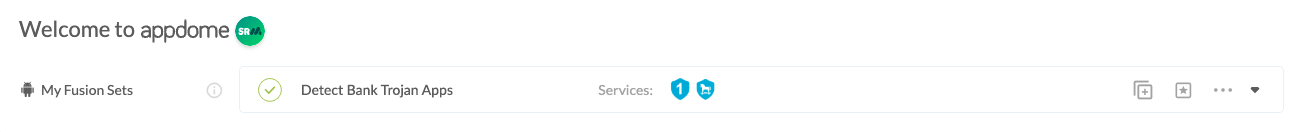
Figure 2: Fusion Set that displays the newly added Protect Android Apps Against Godfather Malware protection
Note: Annotating the Fusion Set to identify the protection(s) selected is optional only (not mandatory). -
Open the Fusion Set Detail Summary by clicking the “...” symbol on the far-right corner of the Fusion Set. Copy the Fusion Set ID from the Fusion Set Detail Summary (as shown below):
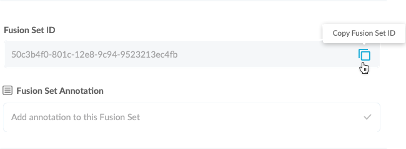
Figure 3: Fusion Set Detail Summary
-
Follow the instructions below to use the Fusion Set ID inside any standard mobile DevOps or CI/CD toolkit like Bitrise, Jenkins, Travis, Team City, Circle CI or other system:
-
Refer to the Appdome API Reference Guide for API building instructions.
-
Look for sample APIs in Appdome’s GitHub Repository.
-
Create and name the Fusion Set (security template) that will contain the Protect Android Apps Against Godfather Malware feature as shown below: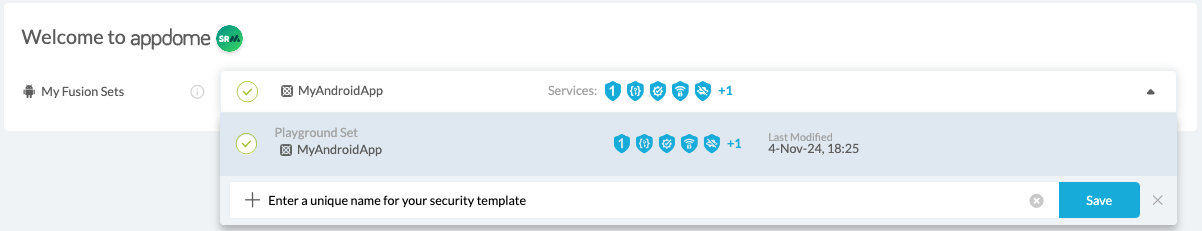
Figure 1: Fusion Set that will contain the Protect Android Apps Against Godfather Malware feature
-
-
Add the Protect Android Apps Against Godfather Malware feature to your security template.
-
Navigate to Build > Anti ATO tab > Banking Trojans section in the Appdome Console.
-
Toggle On Detect Bank Trojan Apps > Protect Android Apps Against Godfather Malware.
Note: The checkmark feature Protect Android Apps Against Godfather Malware is enabled by default, as shown below.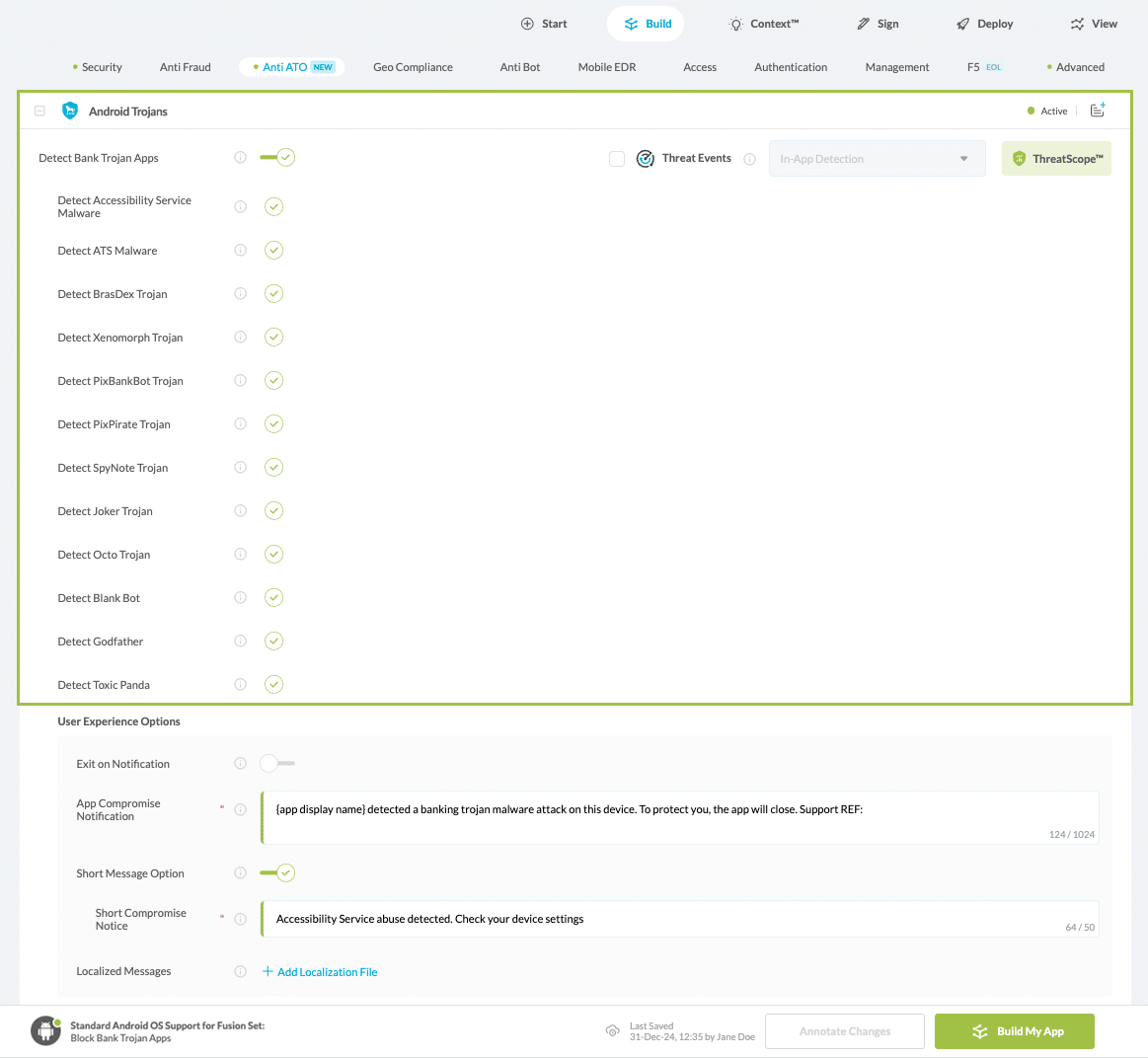
Figure 4: Selecting Protect Godfather Malware
-
Congratulations! The Protect Android Apps Against Godfather Malware protection is now added to the mobile app -
-
Certify the Protect Android Apps Against Godfather Malware feature in Android Apps
After building Protect Android Apps Against Godfather Malware, Appdome generates a Certified Secure™ certificate to guarantee that the Protect Android Apps Against Godfather Malware protection has been added and is protecting the app. To verify that the Protect Android Apps Against Godfather Malware protection has been added to the mobile app, locate the protection in the Certified Secure™ certificate as shown below:
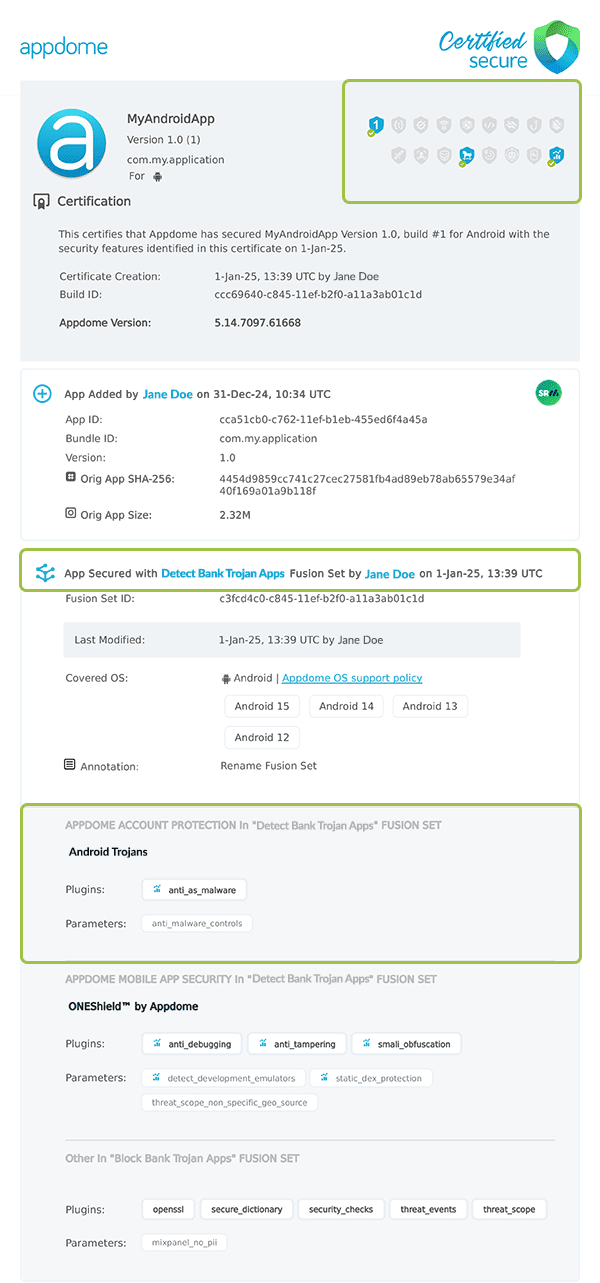
Figure 5: Certified Secure™ certificate
Each Certified Secure™ certificate provides DevOps and DevSecOps organizations the entire workflow summary, audit trail of each build, and proof of protection that Protect Android Apps Against Godfather Malware has been added to each Android app. Certified Secure provides instant and in-line DevSecOps compliance certification that Protect Android Apps Against Godfather Malware and other mobile app security features are in each build of the mobile app.
Using Appdome, there are no development or coding prerequisites to build secured Android Apps by using Protect Android Apps Against Godfather Malware. There is no SDK and no library to code or implement in the app and no gateway to deploy in your network. All protections are built into each app and the resulting app is self-defending and self-protecting.
Releasing and Publishing Mobile Apps with Protect Android Apps Against Godfather Malware
After successfully securing your app by using Appdome, there are several available options to complete your project, depending on your app lifecycle or workflow. These include:
- Customizing, Configuring & Branding Secure Mobile Apps.
- Deploying/Publishing Secure mobile apps to Public or Private app stores.
- Releasing Secured Android & iOS Apps built on Appdome.
Related Articles:
- Prevent ATS Malware in Android Apps
- How to Protect Android Apps Against BrasDex Malware
- How to Detect Xenomorph Trojan in Android Apps
How Do I Learn More?
If you have any questions, please send them our way at support.appdome.com or via the chat window on the Appdome platform.
Thank you!
Thanks for visiting Appdome! Our mission is to secure every app on the planet by making mobile app security easy. We hope we’re living up to the mission with your project.
