Understanding ThreatScope Mobile XTM
Intro
ThreatScope Mobile XTM offers insight into the actual attacks and threats faced by Appdome-protected apps once they’re released into production. The dashboard’s data refreshes every 24 hours, allowing security teams to monitor evolving attacks and swiftly respond to emerging trends in real-time. To ensure that threats faced by a protected app are displayed on the dashboard, there’s no need for prerequisites, API integrations by the Operations teams, or code changes by the mobile development teams.
Setting up Access to ThreatScope Dashboard
Access to a protected app’s threat data on the ThreatScope Dashboard is gated only to viewer accounts that meet the following conditions:
- The viewer account is licensed to access the ThreatScope Dashboard
Submit a request to Appdome support to activate the license for the accounts that should have access to threat data. - Threat data originates from teams of which the viewer is a member.
The team leader of each production team should configure the viewer account. For details, see the section Configuring the Viewer Account. - The viewer has the View ThreatScope entitlement in the team.
For more details, see the section Add View ThreatScope Entitlement to Members Account below.
Configuring the Viewer Account
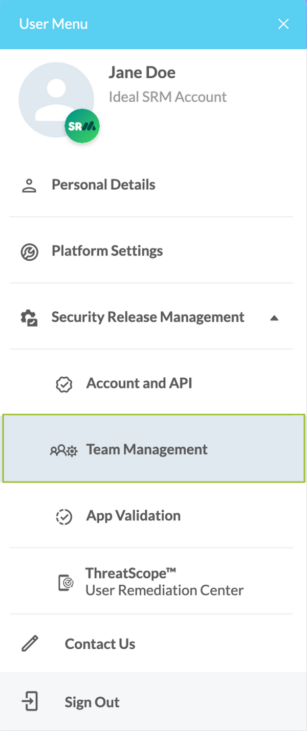
To configure the viewer account, the team leader needs to:
- Open the User Menu.
- Click on Team Management.
- Search for the relevant team.
-
Review the team member list.
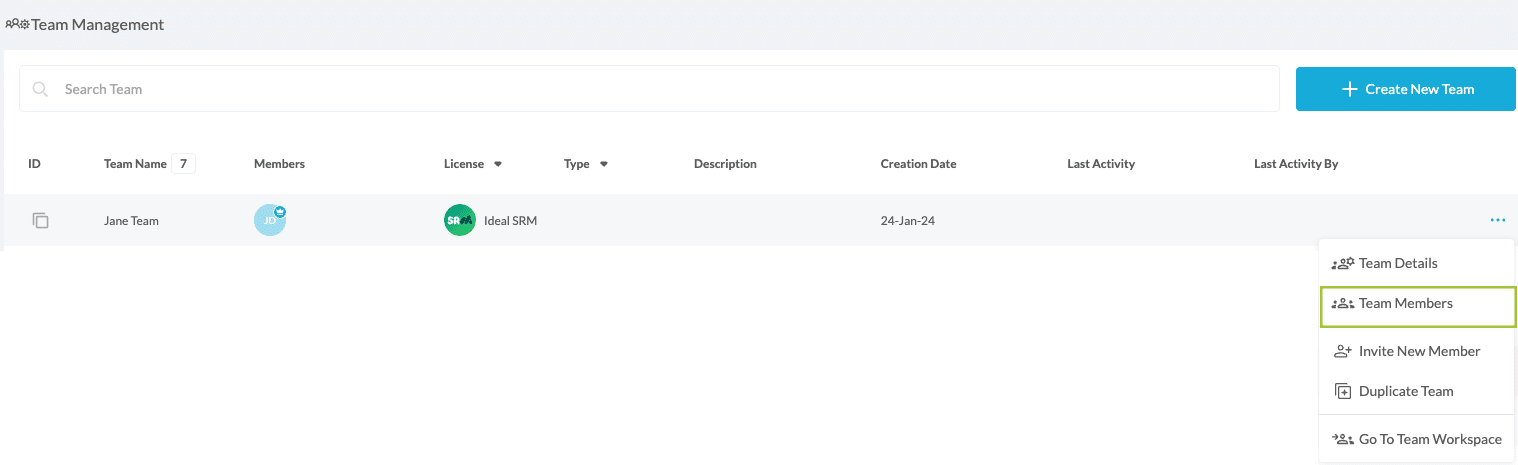
If the requested viewer’s account does not appear, invite the viewer by clicking the Invite New Member button.
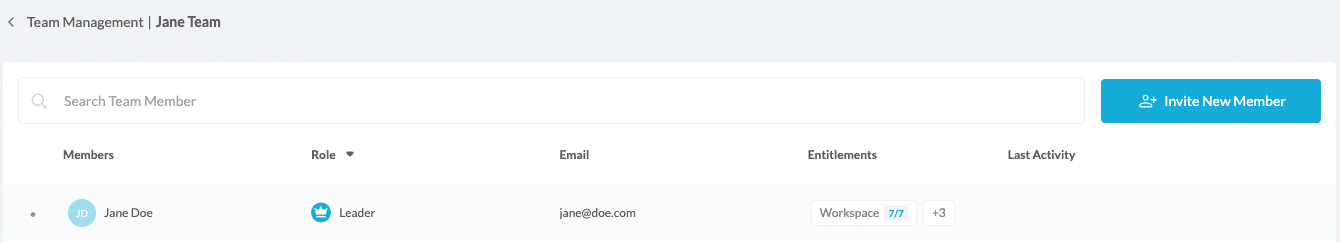
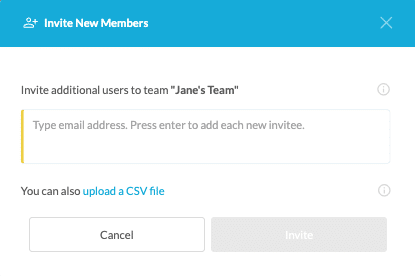
- Type the viewer account’s name and hit enter. When done, click Invite.
- After the viewer accepts the invitation, proceed to the next step of adding the required entitlements to the team.
Add View ThreatScope Entitlement to Members Account
In order to add the View ThreatScope entitlement to a member’s account of a production team, the team leader should follow these steps:
- Click on Team Management account in the user menu and click the button to add entitlements.
A list of the entitlements available for the account will be displayed. - Click the View ThreatScope entitlement.

Reviewing the Dashboard Structure
The dashboard allows you to perform the following tasks:
- Select the viewing scope
- Select the date range
- Review the geographical source of threats
- View all attacks
- Use the Threat Stream widget
- Display top 10 defense breakdown
- View Attacks Breakdown
- Filter Missing Intelligence
- Review threat streams
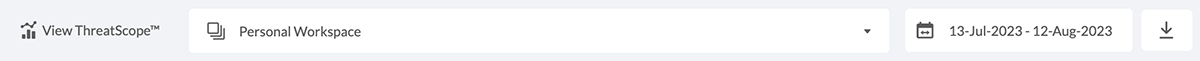
Selecting the Viewing Scope
The dashboard viewer allows defining the scope of data items (threats) to be displayed from the following options:
- A specific team
View only threats associated with apps built by the selected team
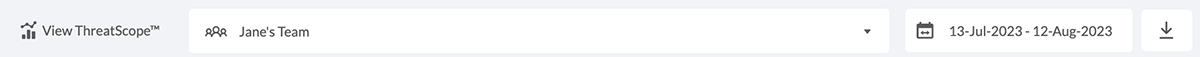
- All my teams
View threats associated with apps built by all teams that the ThreatScope viewer is entitled to access
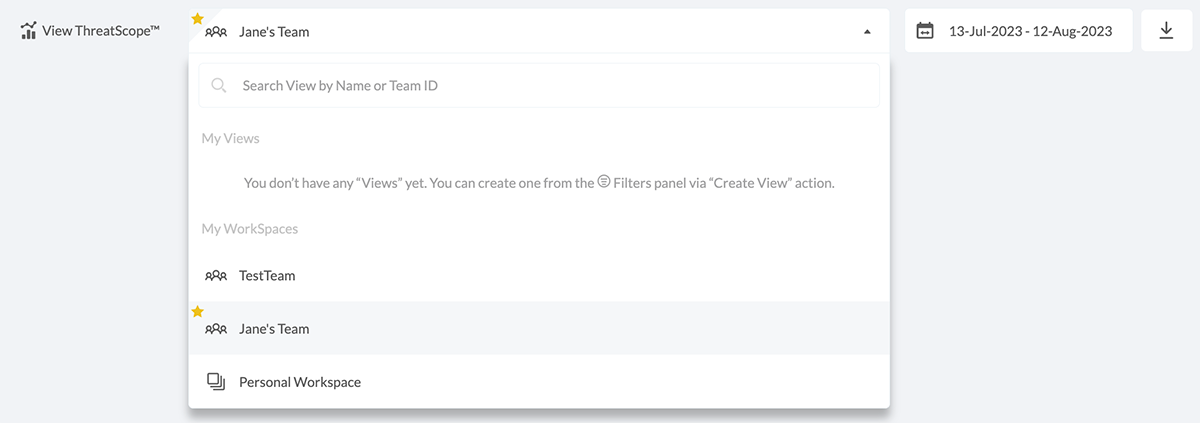
- Personal workspace
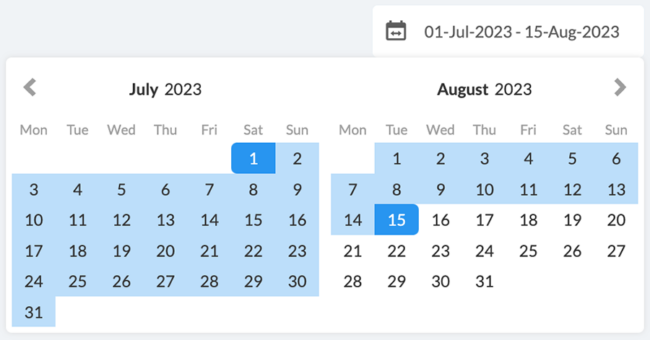
Selecting the Date Range
The Set Date Range section defines the date range of data items (threats) to be displayed. By default, the date range is set to the last 30 days, but this range can be extended in accordance with the ThreatScope dashboard license.
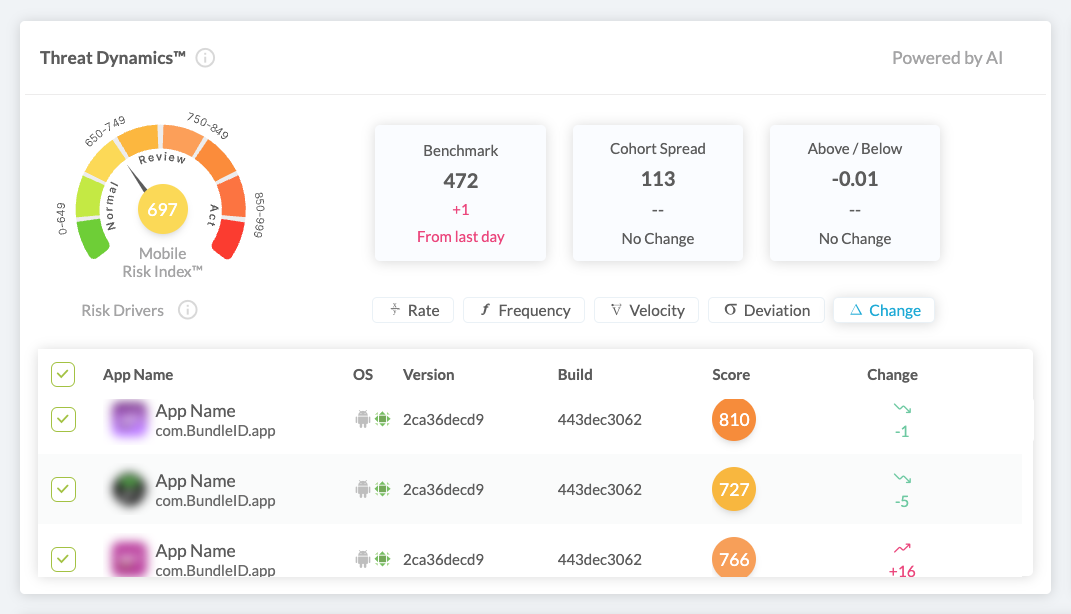
Threat Dynamics™
Threat Dynamics™ uses AI to track how threats evolve within your mobile business, analyzing key risk factors such as infection rate, velocity, frequency, deviation, and change. By leveraging global threat data, it benchmarks your app’s security posture in real time and continuously updates the Mobile Risk Index™, giving you a clear, data-driven view of your app’s risk level.
Click here to learn more about Threat Dynamics™.
Mobile Risk Index™ provides an average Mobile risk index for the selected app(s). If a single app is selected, it displays that app’s specific Mobile risk index, which also appears in the “Score” column of the table below.
Benchmark – Displays the market average Mobile risk index, allowing you to compare your app’s risk level against others. This dynamic score adjusts based on current threat distributions.
Cohort Spread – Shows the range of Mobile risk indexs in similar apps – low spread means consistency, high spread indicates variability.
Above / Below – Shows how your app compares to the global average – negative means stronger security, positive indicates weaker performance.
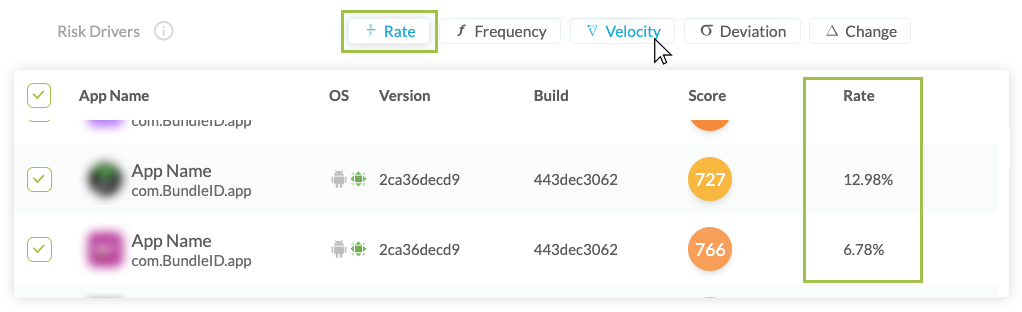
Risk Drivers – Risk Drivers allow you to change metrics such as Infection Rate, Velocity, Frequency, Deviation, and Change to assess whether the risk profile for a threat or app is increasing or decreasing.
By clicking each of the drivers’ buttons you’ll be able to examine the individual metrics for each app in your workspace in the table below.
- Rate – Measures the infection rate by dividing the number of threats by the total number of installations.
- Frequency – Tracks the average number of attack events per app session and measures the net change in the last measurement period.
- Velocity – Measures daily changes in infection rate and attack frequency, showing whether threats are increasing or decreasing compared to the previous day.
- Deviation – Shows daily deviation from the cohort spread, where negative values indicate improvement and positive values signal increased risk.
- Change – Tracks the daily risk score change, where a decrease indicates improvement and an increase signals higher risk.
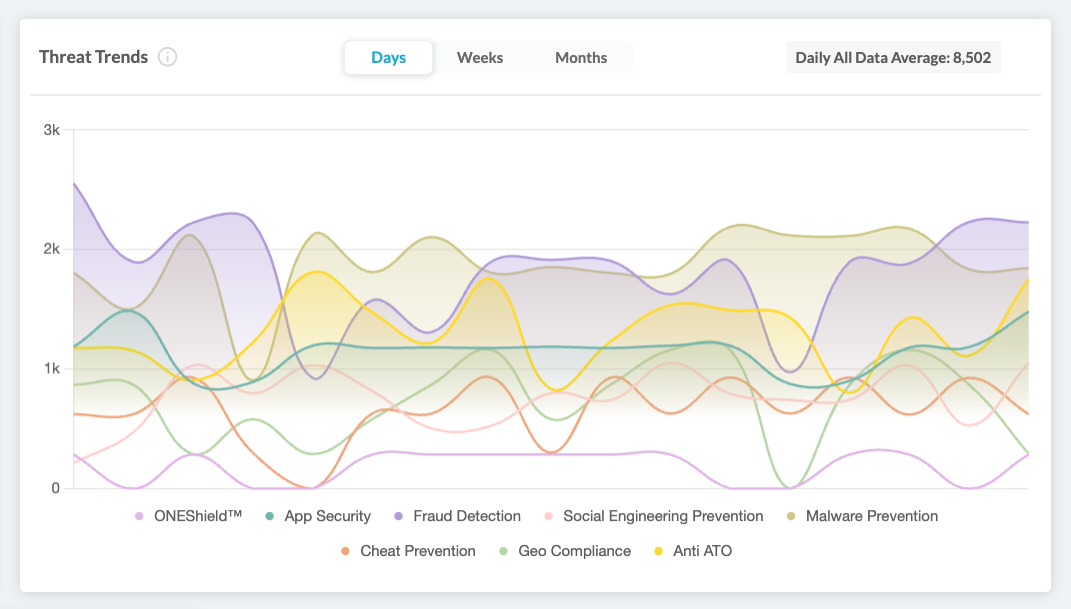
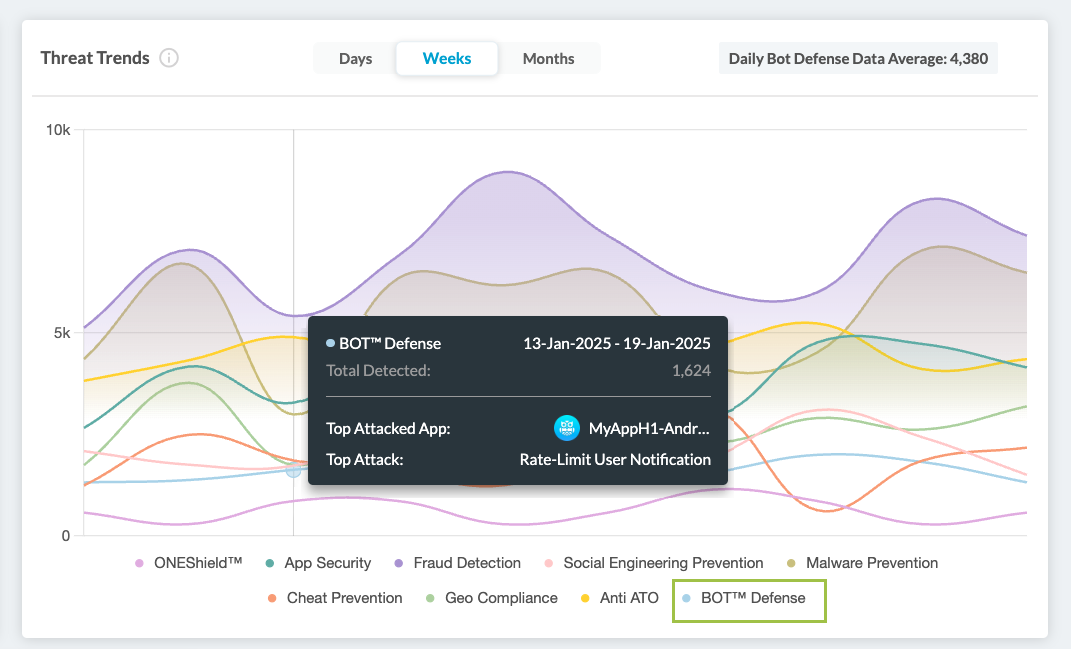
Threat Trends
Threat Trends provides valuable insights into the threats your apps are facing, categorized by Appdome’s protection packages.
Track the evolution of mobile threats over various time frames, including total threats detected, the most attacked app, and the predominant attack methods for each protection package.
Display Options:
- You can explore the data in daily, weekly, or monthly views.
- The color-coded protection packages at the bottom of the display allow you to filter the data by clicking on them to include or exclude specific packages.
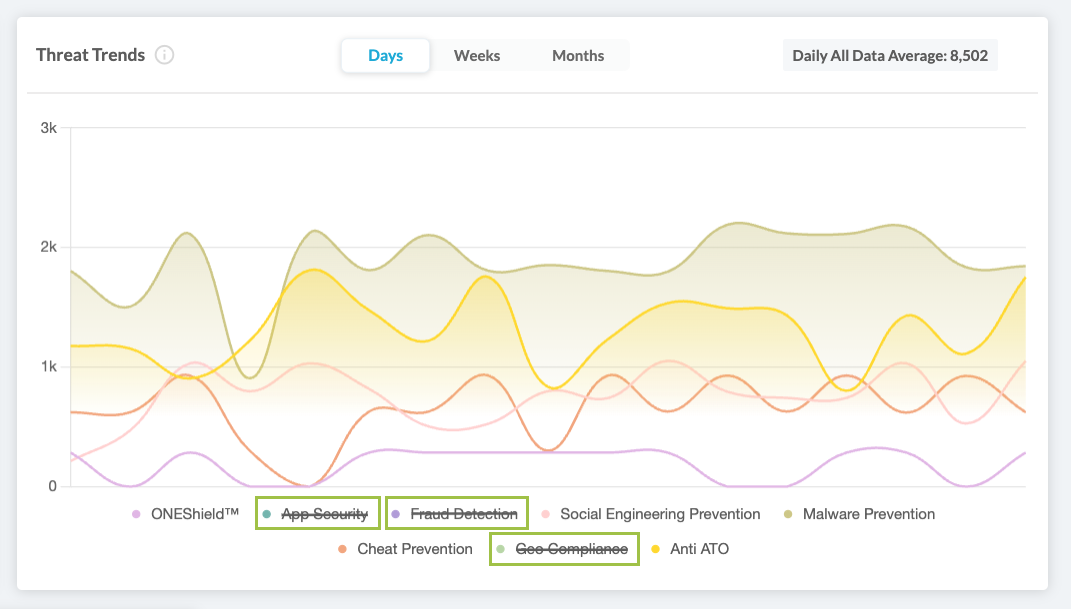
- Hovering over any point in the graph reveals a tooltip with detailed information, including the date or date range, total attacks detected, the top attack method, and the most targeted app.
- Bot Defense Data – When selecting this option from the Threat-Inspect™ menu, it adds the MobileBot data to the Threat Trends display.
Click here to learn more about Appdome’s MobileBOT™ Defense.
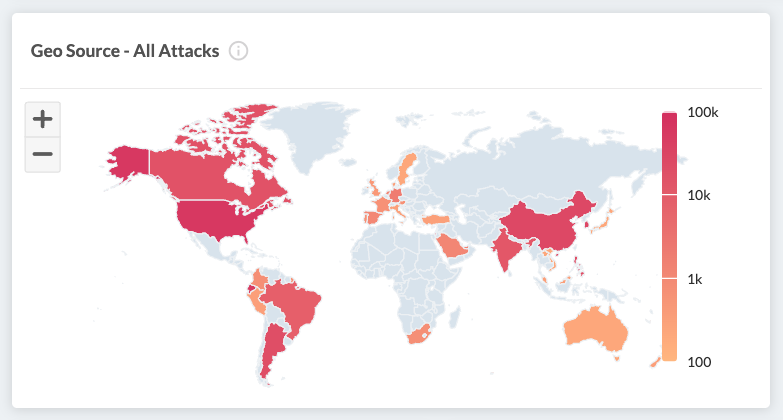
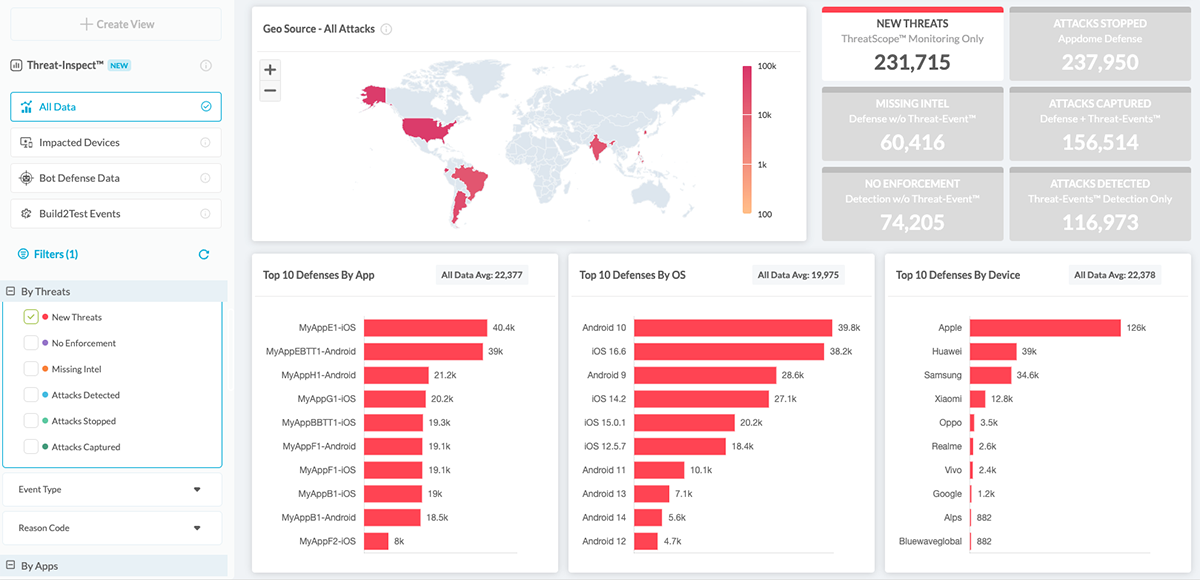
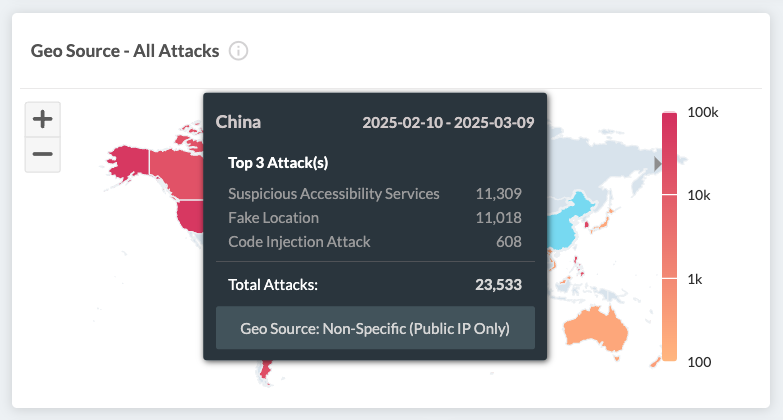
Reviewing the geographical source of threats
The GeoSource section displays a map that allows viewing the country from which the attacks originate.
Countries are colored based on the volume of threats detected in the region. For clarification, see the legend on the right.
Hover over the requested country to see a breakdown of the information by the following items:
- Country name
- Date Range
Only threats from the listed date range are aggregated. - Total attacks
The sum represents all attacks originating from the country over which the mouse hovers. - Top 3 Attacks
The top attacks for the selected country
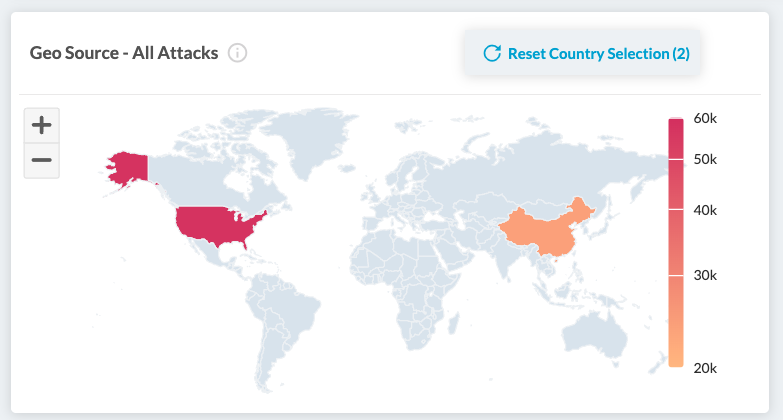
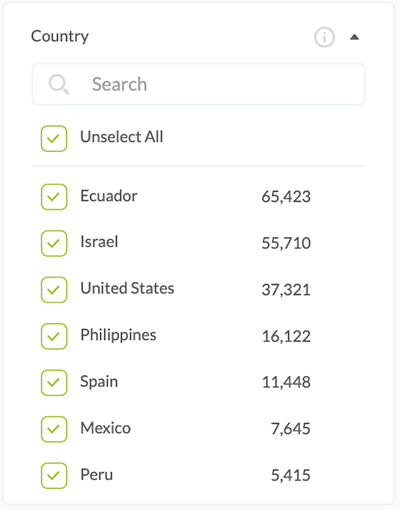
To select one or more countries:
- To select a single country, click the requested country on the map or choose its corresponding checkbox. To deselect a country, click the checkbox of the already selected country.
- To select multiple countries, check the boxes next to each requested country.
- All other ThreatScope displays will update according to the selected countries.
Types of Geography-based data input
The following types of geography-based data input exist:
- Non-specific
The default data input on Appdome relies on the public IP address captured from its analytics server to map the threat’s location. Given that attackers can mask their public IP using tools such as VPNs and proxies, this data is labeled as “non-specific,” namely because we cannot always pinpoint the precise source of an attack.
- Specific
In this case, the data input is the device’s location data (GPS). However, since accessing location data requires declaring specific permission in the app and user consent, this type of threat geo-source is not the default option and requires opting in when building the app on Appdome.
The app’s developer is responsible for adding the required location permissions and requesting user consent to access the device’s location since Appdome will not add location permissions to the protected app and trigger any access to location data without checking if the user has granted access to their location data.
What can be inferred from the data
- Ability to create a focus list of countries that generate the most attacks
Customers that have a web application firewall (WAF) in place can use this data stream to apply different security policies based on the threat landscape of the app and the app’s user base. - Visibility of how the threat types are distributed within a given country
This can enable tracking which vectors are used by different local and global actors. - You can use the Snapshots feature to download the current view of the selected GeoSource.
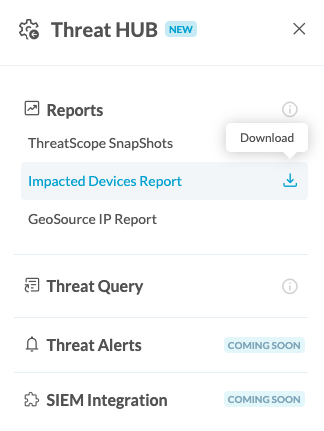
Reviewing Impacted Devices Report
After applying the selected filters, the displayed sum of Threat Events and Attacks represents the accumulation of all events that occurred on a large number of devices.
Each device may experience multiple events, and the distribution of events between devices can result in different insights. For example, if there are 1000 events, but 990 of them occurred on one device, the situation would differ significantly compared to if those 1000 events were spread across 1000 individual devices.
To gain more insights into the distribution of events, Appdome allows users to generate a report that describes how many devices were involved in each of the chosen event types.
- Apply selected ThreatScope filters.
Note: The user must choose at least one specific Event Type or Reason Code in order to produce the report. - Click on the download drop-down button on the top right
- Select Download Impacted Devices report
- The report is downloaded and lists the number of unique devices per event according to the selected filters.
The report will return in JSON format; each object includes the name of the attack and the number of involved devices:
{
"<FAC Event Name #1>": {
"eventType": "< Event externalID>",
"impactedDevices": "< # of unique device IDs for externalID in selected filters>"
},
"<FAC Event Name #2>": {
"eventType": "< Event externalID>",
"impactedDevices": "< # of unique device IDs for externalID in selected filters>”
}
}
Using the Threat Stream widget
The Threat Stream Widget displays the distribution of attacks of the selected date range between the various threat streams.
What can be inferred from the data?
- Evaluate the risk level of released apps
By tracking blocked and app-enforced threats. - Compare intelligence gathered by released apps
With the actual volume of attacks and threats.
Filtering the display
Click on any Threat Stream tile to remove the selected threat stream from the filter. You can adjust the filter to view one or multiple Threat Streams.
You can also apply filters by using the left-side menu.
When you apply a filter using the Threat Stream widgets, the selected category is highlighted in color, and the unselected categories turn gray. This visual distinction helps you easily identify which filters are active while focusing on the data from the selected category.
The filter is applied on the Geo Source and the Top 10 Defenses displays.
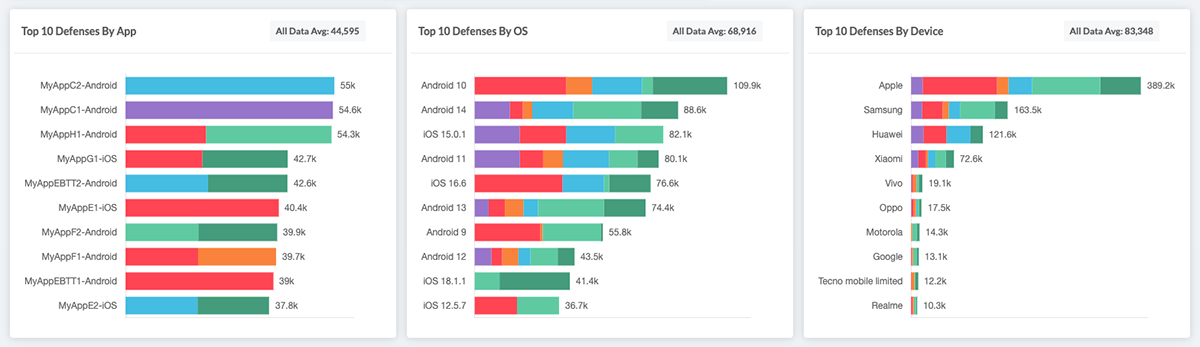
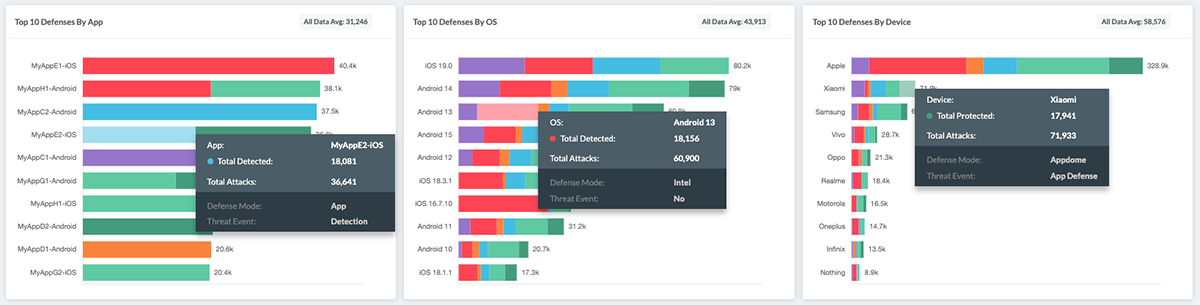
Displaying Top Defenses Breakdown
The Top Defenses section displays a breakdown of the top defenses by app, OS, and manufacturer.
What can be inferred from the data?
The data displayed in this section allows for the generation of a list of the characteristics of the apps and devices that are most targeted by the attacks.
Hover over a graph line in any of the Top Defenses Breakdown tiles to display the following breakdown:
- App/OS/Device
List the top attack’s identifier. - Total Detected/Protected
The value of this field represents the number of attacks and threats associated with the threat stream being hovered in the date range listed in the Date field.
This field name is Total Protected when the trend line relates to threat streams in which Appdome blocked the attack; otherwise, the name is Total Detected. - Defense Mode
See description in section Viewing all attacks. - Threat Event
See description in section Viewing all attacks.
The Average widget
The Average widget is locate on the top of each ‘Top 10’ display, and displays the following information:
- Avg. Attacks per App
It is calculated by dividing the total number of attacks and threats in the Top Defenses By App tile divided by the number of listed apps. - Avg. Attacks per OS
It is calculated by dividing the total number of attacks & threats in the Top Defenses By OS tile divided by the number of listed OS versions. - Avg. Attacks per Device
It is calculated by dividing the total number of attacks & threats in the Top Defenses By Device tile divided by the number of listed manufacturers.
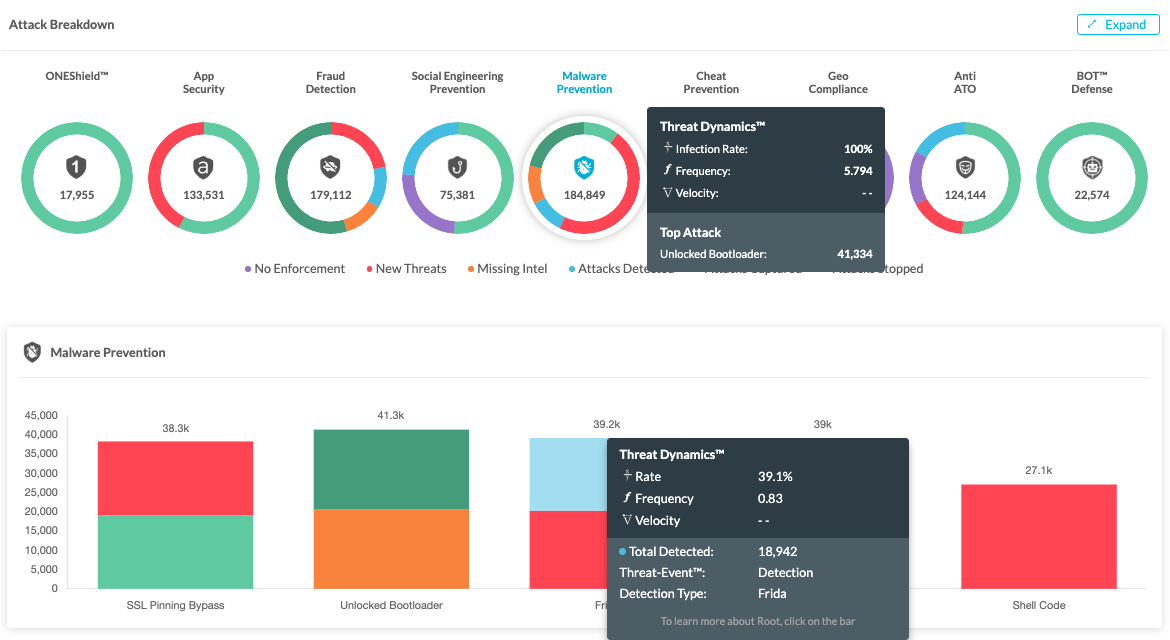
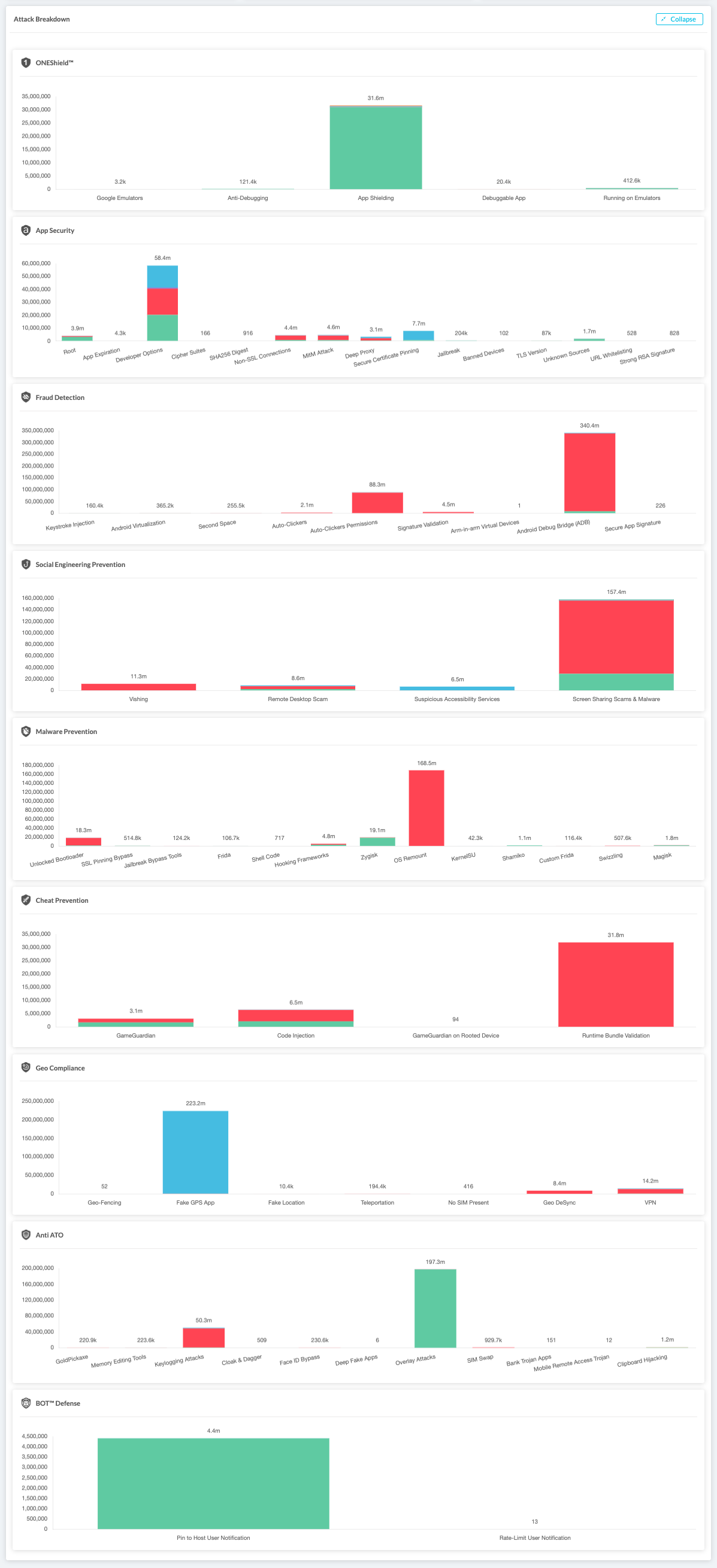
Attacks Breakdown
The Attacks Breakdown displays the attacks divided by Threat type:
- ONEShield™ by Appdome
- Mobile App Security
- Mobile Fraud Detection
- Social Engineering Prevention
- Malware Prevention
- Cheat Prevention
- Geo Compliance
- Anti ATO
- BOT™ Defense
The default view, as shown below, displays the group with the most events. You can change the display by clicking on any of the other doughnut graphs to display the data breakdown for that group:
Note: When hovering over each Threat Type graph, the tooltip will display the Treat Dynamics info. On the top display the information is for the entire Appdome Protection Package and in the detailed display below it shows the data for each threat.
Expanding the Attacks Breakdown
To view the detailed display for all attack types, click on the ‘Expand’ button at the top right corner to expand the display of all Event types. ![]()
Collapse the display back to default mode by clicking on ‘Collapse.’ ![]()
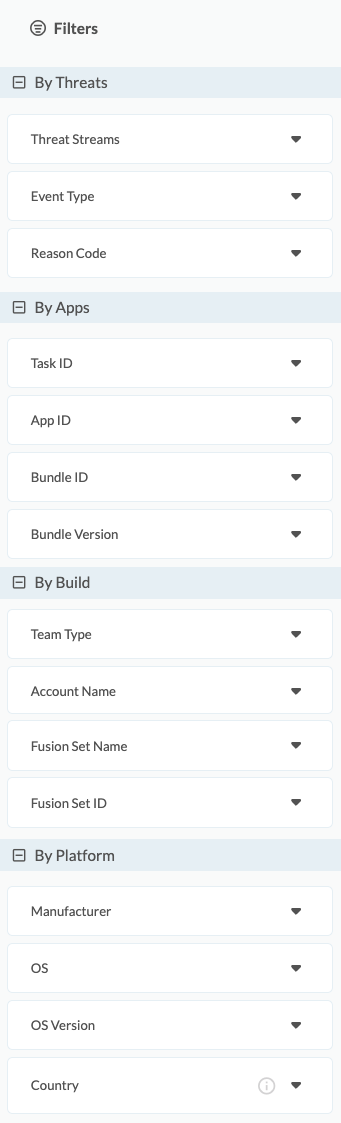
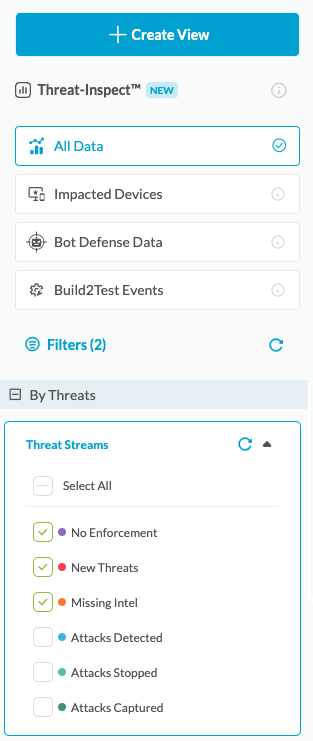
Filtering Threat Intelligence
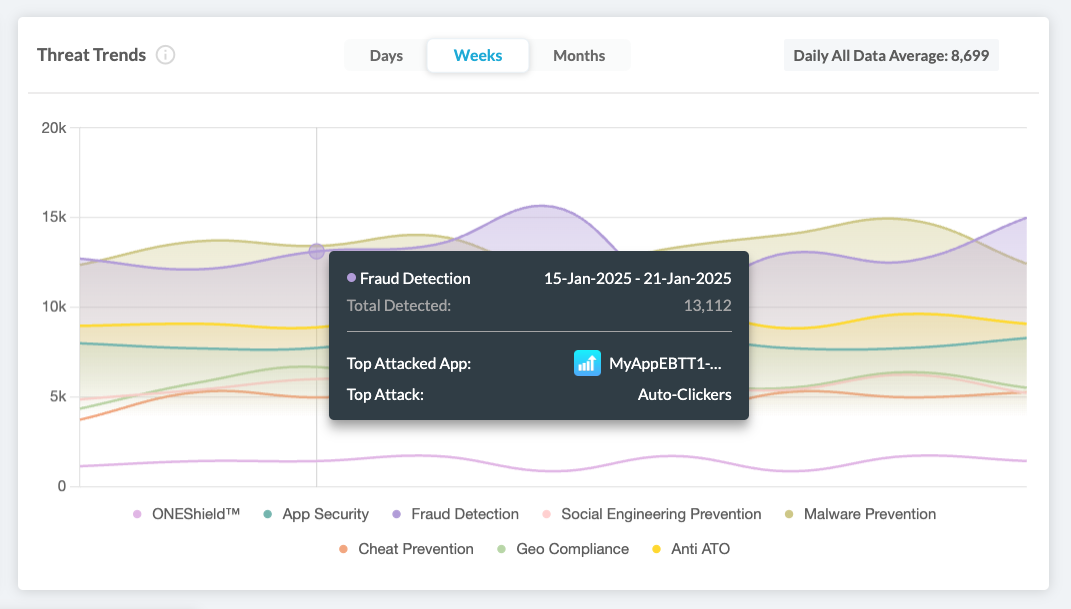
Threat-Inspect™
The Threat-Inspect™ menu on the left side panel enables easy filtering and creation of custom views for the Threat Scope data.
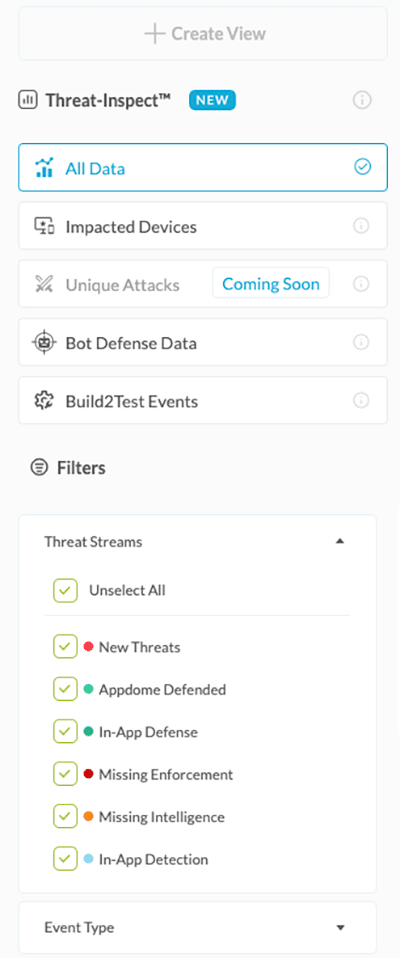
1. Select the Data displayed from one of the following categories

All Data – Displays all accumulated data by the number of individual events. If a specific device experiences several events of the same type, all events will be counted.

Impacted Devices – Summarizes the number of unique devices on which any event occurred. If one specific device experiences a particular event a number of times, it will still be counted as one device.

Bot Defense Data—Access complete payload data from Appdome’s MobileBOT™ Defense (MBD) solution for insights on mobile infrastructure. Correlating and validating real attacks can detect and prevent attacks like credential stuffing and DDoS.

Build2Test Events—This function summarizes the Threat Events data only for apps built with the Build-to-Test feature. These apps are built specifically for testing via third-party vendors.
Learn more about Appdome’s Build-to-Test
2. Filter the data
You can filter the data using any of the following filters and combine them to create unique views, gaining deeper insights into the events your Appdome-built apps are facing.
The filters that can be used for controlling the displayed data are:
- By Threats
- Threat Stream – The type of defense implemented in Threat Events.
- By Apps
- Task ID – The unique ID of the task (upload/build/context/sign)
- App ID – The unique ID of the app.
- Bundle ID – The app’s identifier is listed in the AndroidManifest.xml or Info.plist file.
- Bundle Version – The app’s version number.
- By Build
- Team Type
- Account Name – The Name of the account owner.
- Fusion Set Name – The name of the fusion set to which the protected app is subscribed.
- Fusion Set ID – The ID of the fusion set to which the protected app is subscribed.
- By Platform
- Manufacturer – The device manufacturer associated with the detected attack.
- OS – The platform related to the detected attack.
- OS Version – The OS Version associated with the detected attack
- Country – A specific Geo Source.
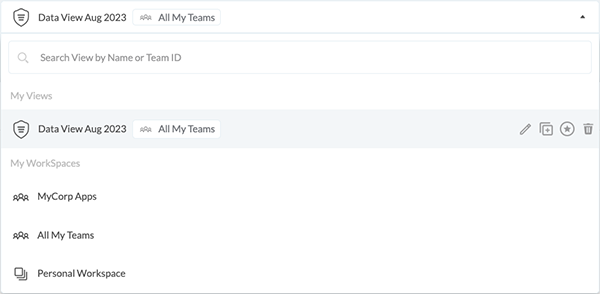
3. Create View
When the data is filtered, you can save it by creating a view.
You can access your custom views via the main drop-down menu.
Learn more about Threat Inspect.
Filtering by Specific Builds
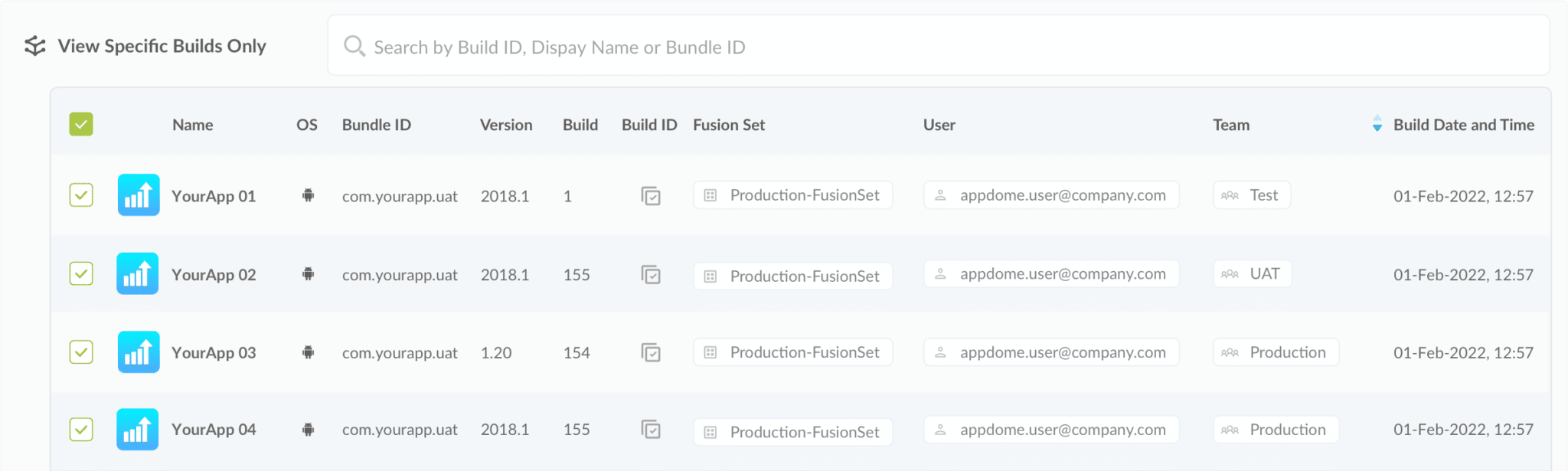
The section View Specific Builds with Threats Only allows:
- A filter is applied to the ThreatScope by using specific builds of protected apps.
- The viewer can find a specific build using the search bar by looking for any of the attributes shown below. The tile filter is synchronized with the filter pane. For further information, see the Filter Pane section.
- Scrolling through the list of protected apps associated with the attacks & threats shown in the dashboard. The Build ID of the danger can be copied by clicking on the copy icon
 ;
;
Avg. Attack Widgets
In some cases, it is useful to get a sense of the baseline of attacks and threats to which the app is exposed. Comparing the current volume of threats to the average line to identify anomalies helps to determine when the protected app is being actively attacked as part of a focused campaign.
Troubleshooting Access to ThreatScope Dashboard
This section provides troubleshooting information for resolving the following issues:
- Lack of the View ThreatScope entitlement.
- The viewer is a member of a team but does not have the View ThreatScope entitlement.
- The viewer is not a member of any team.
- The viewer or View ThreatScope entitlement was removed.
- If the viewer was a member of a team or had view entitlements, then the viewer was removed from the team or the view entitlement was removed.
Lack of the View ThreatScope entitlement
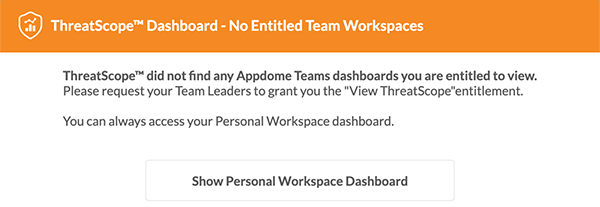
Cause:
The viewer attempted to access the ThreatScope dashboard, but while the viewer’s account is a member of at least one team, that team does not have View ThreatScope entitlement permissions.
Remediation:
Add the View ThreatScope entitlement to each team to give the viewer access to threat data. For additional information, see the section on Setting up access to ThreatScope Dashboard.
Viewer is not a member of any team
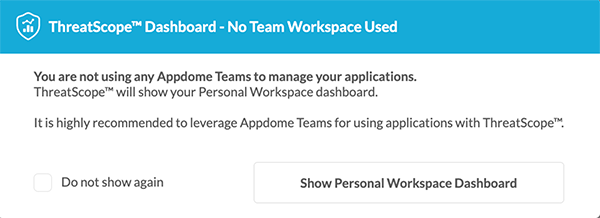
Cause:
The viewer tried to access the ThreatScope dashboard by using the All My Teams workspace, but the viewer’s account is not a member of any team.
Remediation:
Request the production team leader to invite the viewer’s account to join the team and add the View ThreatScope entitlement to each team so that the viewer can access the threat data. For further information, see the section Setting up access to the ThreatScope Dashboard.
A viewer or View ThreatScope entitlement was removed
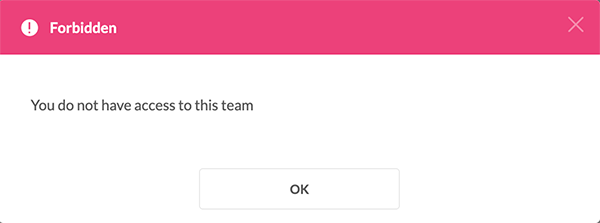
Cause:
The viewer tried to access a team in the ThreatScope dashboard; however, the viewer’s account was removed from that team, or the View ThreatScope entitlement was removed from the viewer’s account in that team.
Remediation:
Request the production team leader to invite the viewer’s account to join the team and add the View ThreatScope entitlement to each team so that the viewer can access the threat data. For further information, see the section Setting up access to ThreatScope Dashboard.
Related Articles
- How to use ThreatScope™ – Threat Dynamics
- Threat-Events™, In-App Threat Intelligence in Native iOS Apps
- How to Use ThreatScope™ User Remediation Center
- Understanding ThreatScope Views
How Do I Learn More?
If you have any questions, please send them our way at support.appdome.com or via the chat window on the Appdome platform.
Thank you!
Thanks for visiting Appdome! Our mission is to secure every app on the planet by making mobile app security easy. We hope we’re living up to the mission with your project.