Binary Code Obfuscation, Anti-Reversing - Android & iOS
Learn to Prevent Code Obfuscation in Mobile apps, in mobile CI/CD with a Data-Driven DevSecOps™ build system.
Why is Obfuscation Efficient Against Reverse Engineering?
How does Appdome Implement Binary Code Obfuscation?
In iOS, the application’s executable manifests as binary code. Appdome shuffles the code around, so that when the reverse engineering tool attempts to determine the target of a reference, it will appear as though it points to some arbitrary location. On a large scale, this renders the code completely unintelligible. However, the application must contain enough binary code to make the shuffling effective, otherwise it is advisable to use Appdome Flow Relocation as an alternative.
In Android, shared-libraries constitute the native-code part of the app. Appdome uses the loading mechanism of shared libraries in Android and modifies it so encrypted libraries can be loaded. Then, when integrating Binary Code Obfuscation, the native libraries that come with the application get encrypted by using a unique key.
When an attacker attempts to open the protected libraries in a reverse engineering tool, the applications will fail at recognizing the file as binary code.
Prerequisites for Using Binary Code Obfuscation:
To use Appdome’s mobile app security build system to Prevent Code Obfuscation , you’ll need:
- Appdome account (create a free Appdome account here)
- A license for Binary Code Obfuscation
- Mobile App (.ipa for iOS, or .apk or .aab for Android)
- Signing Credentials (see Signing Secure Android apps and Signing Secure iOS apps)
Prevent Code Obfuscation on Mobile apps using Appdome
On Appdome, follow these 3 simple steps to create self-defending Mobile Apps that Prevent Code Obfuscation without an SDK or gateway:
-
Upload the Mobile App to Appdome.
-
Upload an app to Appdome’s Mobile App Security Build System
-
Upload Method: Appdome Console or DEV-API
-
Mobile App Formats: .ipa for iOS, or .apk or .aab for Android
-
Binary Code Obfuscation Compatible With: Obj-C, C+, Java, JS, C#, C++, Swift, Kotlin, Flutter, React Native, Unity, Xamarin, and more
-
-
Build the feature: Binary Code Obfuscation.
-
Building Binary Code Obfuscation by using Appdome’s DEV-API:
-
Create and name the Fusion Set (security template) that will contain the Binary Code Obfuscation feature as shown below:
-
Follow the steps in Sections 2.2.1-2.2.2 of this article, Building the Binary Code Obfuscation feature via Appdome Console, to add the Binary Code Obfuscation feature to this Fusion Set.
-
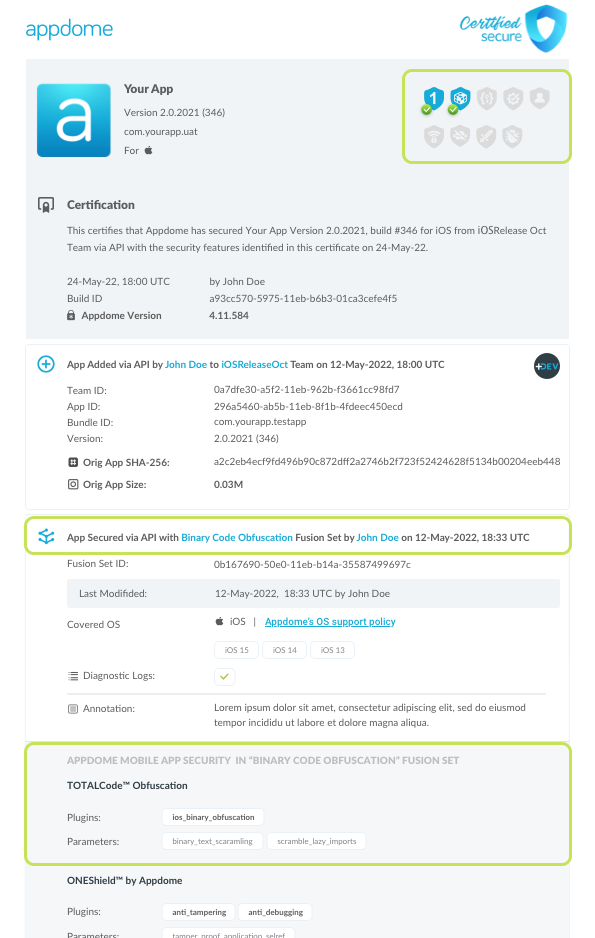
Open the Fusion Set Detail Summary by clicking the “...” symbol on the far-right corner of the Fusion Set, as shown in Figure 1 above, and get the Fusion Set ID from the Fusion Set Detail Summary (as shown below):
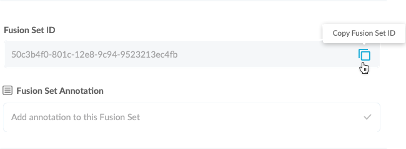
Figure 2: Fusion Set Detail Summary
Note: Annotating the Fusion Set to identify the protection(s) selected is optional only (not mandatory). -
Follow the instructions below to use the Fusion Set ID inside any standard mobile DevOps or CI/CD toolkit like Bitrise, App Center, Jenkins, Travis, Team City, Cirlce CI or other system:
-
Build an API for the app – for instructions, see the tasks under Appdome API Reference Guide
-
Look for sample APIs in Appdome’s GitHub Repository
-
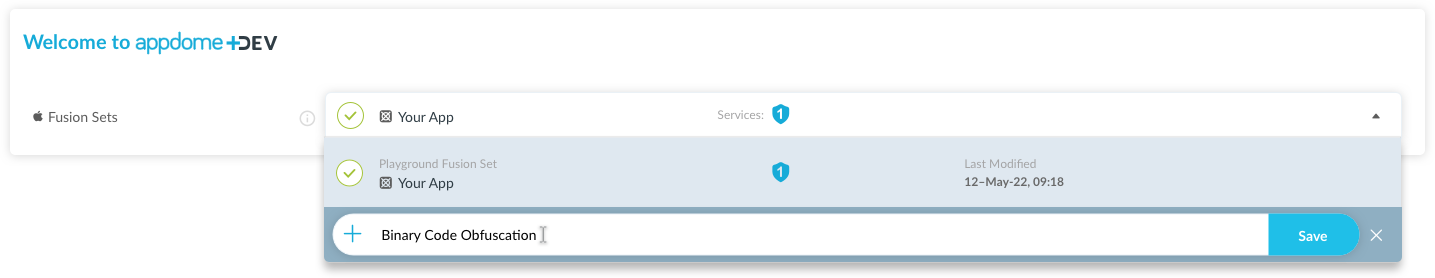
Figure 1: Fusion Set that will contain the Binary Code Obfuscation feature
Note: Naming the Fusion Set to correspond to the protection(s) selected is for illustration purposes only (not required). -
-
Building the Binary Code Obfuscation feature via Appdome Console
To build the Binary Code Obfuscation protection by using Appdome Console, follow the instructions below.
-
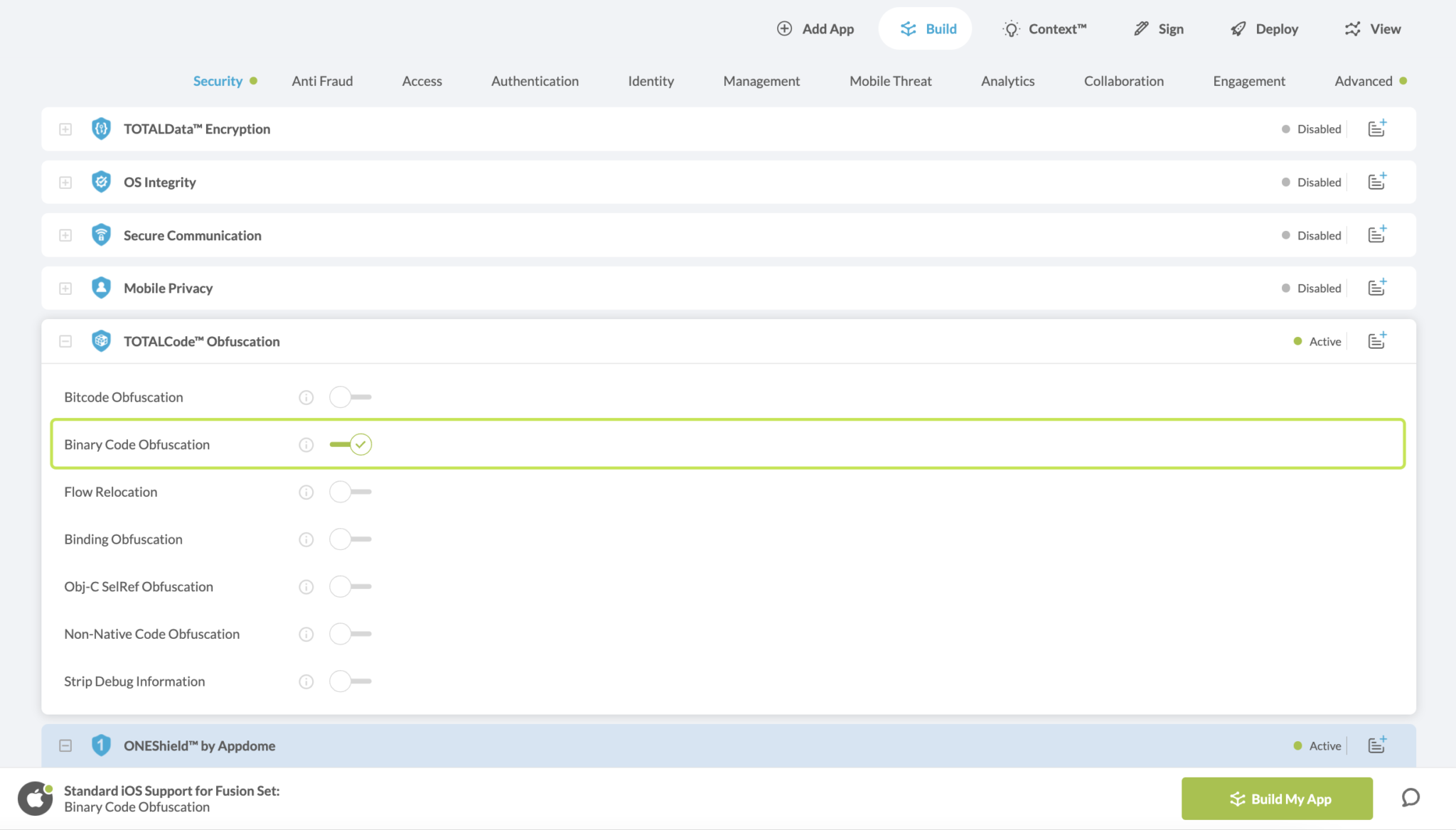
Where: Inside the Appdome Console, go to Build > Security Tab > TOTALCode™ Obfuscation section.
-
When you select the Binary Code Obfuscation you'll notice that your Fusion Set you created in step 2.1.1 now bears the icon of the protection category that contains Binary Code Obfuscation
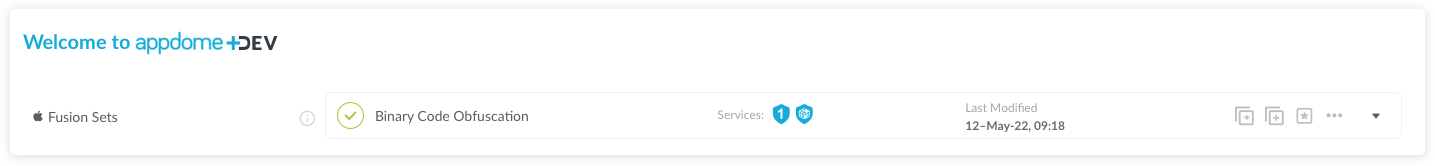
Figure 4: Fusion Set that displays the newly added Binary Code Obfuscation protection
- Extra Configuration with Binary Code Obfuscation:
- Favor App’s Size
Automatically detect and exclude publicly available elements from being obfuscated, to reduce overall application package size.
-
Click Build My App at the bottom of the Build Workflow (shown in Figure 3).
-
Congratulations! The Binary Code Obfuscation protection is now added to the mobile app -
Using Appdome, there are no development or coding prerequisites to build secured Mobile Apps by using Binary Code Obfuscation. There is no SDK and no library to code or implement in the app and no gateway to deploy in your network. All protections are built into each app and the resulting app is self-defending and self-protecting.
Releasing and Publishing Mobile Apps with Binary Code Obfuscation
After successfully securing your app by using Appdome, there are several available options to complete your project, depending on your app lifecycle or workflow. These include:
- Customizing, Configuring & Branding Secure Mobile Apps
- Deploying/Publishing Secure mobile apps to Public or Private app stores
- Releasing Secured Android & iOS Apps built on Appdome.
Related Articles:
- Non-Native Code Obfuscation, Anti-Reversing for Android & iOS Frameworks
- Obfuscate Mobile Business Logic, Anti-Reversing in Android & iOS Apps
- Dex Control Flow Relocation, Anti-Reversing for Android Apps
If you have any questions, please send them our way at support.appdome.com or via the chat window on the Appdome platform.
Thank you!
Thanks for visiting Appdome! Our mission is to secure every app on the planet by making mobile app security easy. We hope we’re living up to the mission with your project.