How to Secure Android & iOS Apps in GitHub CI/CD Pipelines
This Knowledge Base article provides clear instructions on how to use the Appdome Build-2Secure plugin within GitHub CI/CD pipelines to seamlessly secure, sign, and certify mobile apps.
What is Appdome Build-2Secure?
Appdome’s Build-2Secure plugin is an out-of-the-box CI/CD integration, making it easy for mobile developers to automate the building, signing, and certification of security, anti-fraud, and other protections in Android & iOS apps in GitHub CI/CD pipelines.No code or SDKs are required.
Appdome’s Build-2Secure plugin streamlines cyber and anti-fraud protections within CI/CD pipelines by automating three essential steps:
For more general information on GitHub Actions, refer to the GitHub Actions Documentation
Prerequisites
- An Appdome SRM account
- Appdome API token
- Fusion-Set ID
- A GitHub Account. If you do not have an existing account, you can create one on the GitHub website.
- A GitHub repository.
- Ensure you have a .YML file in the path repository/.github/workflows/*.yml
- Optional: A Firebase Crashlytics account
Step-by-Step Guide for Using Appdome Build-2Secure Plugin in GitHub
Step 1: Add Appdome GitHub Action to Your CI/CD Workflow
- Edit your GitHub workflow file: Open the .yml workflow file located at repository/.github/workflows/<workflow_file>.yml
If you don’t have a workflow, follow the GitHub Actions Quickstart to create one.
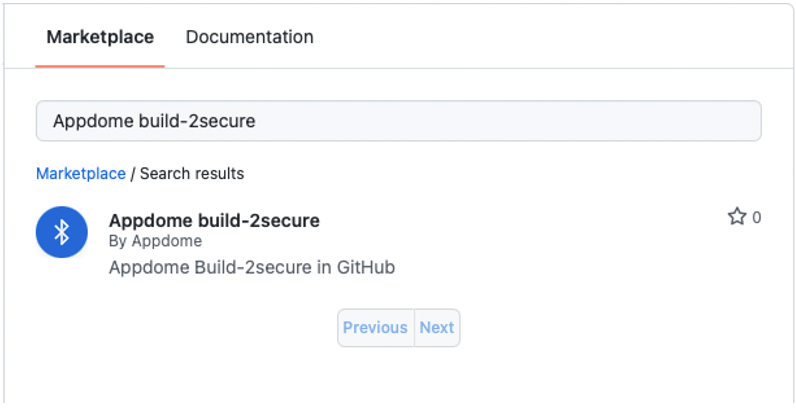
Note: The Build-2Secure Action requires a built app to function. - Open the Marketplace tab and search for “Appdome Build-2Secure”.
Step 2: Store and Manage Secrets in GitHub
Secrets are encrypted variables you create in an organization, repository, or environment. They are crucial for securely handling sensitive information like API tokens and keystore passwords in GitHub Actions workflows. Learn more about using secrets in GitHub Actions.
Optional: Store all your sensitive variables in GitHub’s encrypted secrets for the repository.
While optional, it is highly recommended that you store your sensitive information as encrypted secrets for additional security. Follow these steps:
- Define the variables of secrets as follows:
- Create a secret name SECRET_EXAMPLE.
- In the secret field, enter the value of SECRET_EXAMPLE.
- Now it can be encrypted called as ${{ secrets.SECRET_EXAMPLE }}
- Optional: Store your KEYSTORE_FILE as base64 value on secrets by following these steps:
- Create a secret name KEYSTORE_BASE64
- Enter the following command in the terminal:
base64 -i your_keystore.keystore -o keystore_base64.txt - Copy the content of the text file to the secret field.
- The text file can now be referred to as ${{ secrets.KEYSTORE_BASE64 }};
- After the workflow file is ready, click start commit, then commit a new file.
- Repeat the above process for all file fields in the yml file.
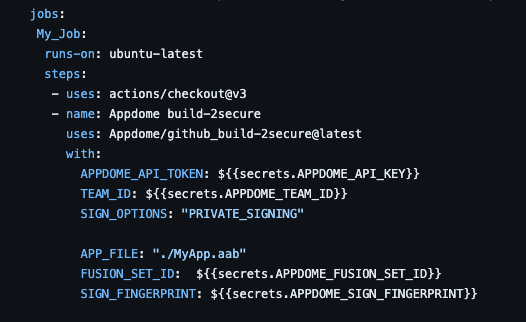
Step 3: Running the Appdome Build-2Secure Action
To run the Appdome Build-2Secure action:
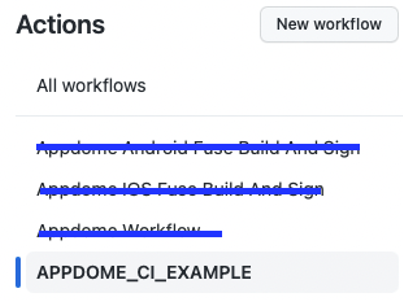
- Navigate to the Actions tab.
- Select your workflow from the Actions list.
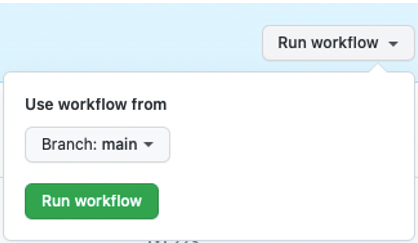
- Expand the Run workflow dropdown and click Run workflow to initiate the action.
- Once the build is complete, you can download the secured app from the Artifacts tab.
Step 4: Access the Appdome-Secured app
After running the workflow, you can find the Appdome secured app under the following name:
${{ env.APPDOME_SECURED_APP }}
Note: The additional universal apk file for the second output option described above can be found under the following name:
${{ env.APPDOME_SECURED_APP_SECOND_OUTPUT }}
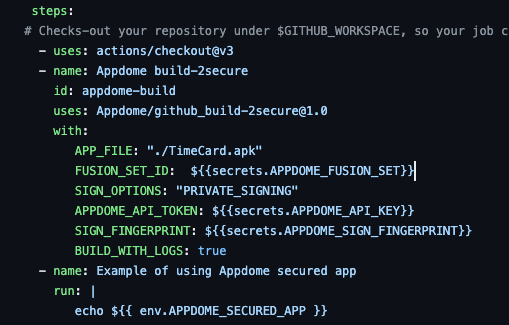
For example:
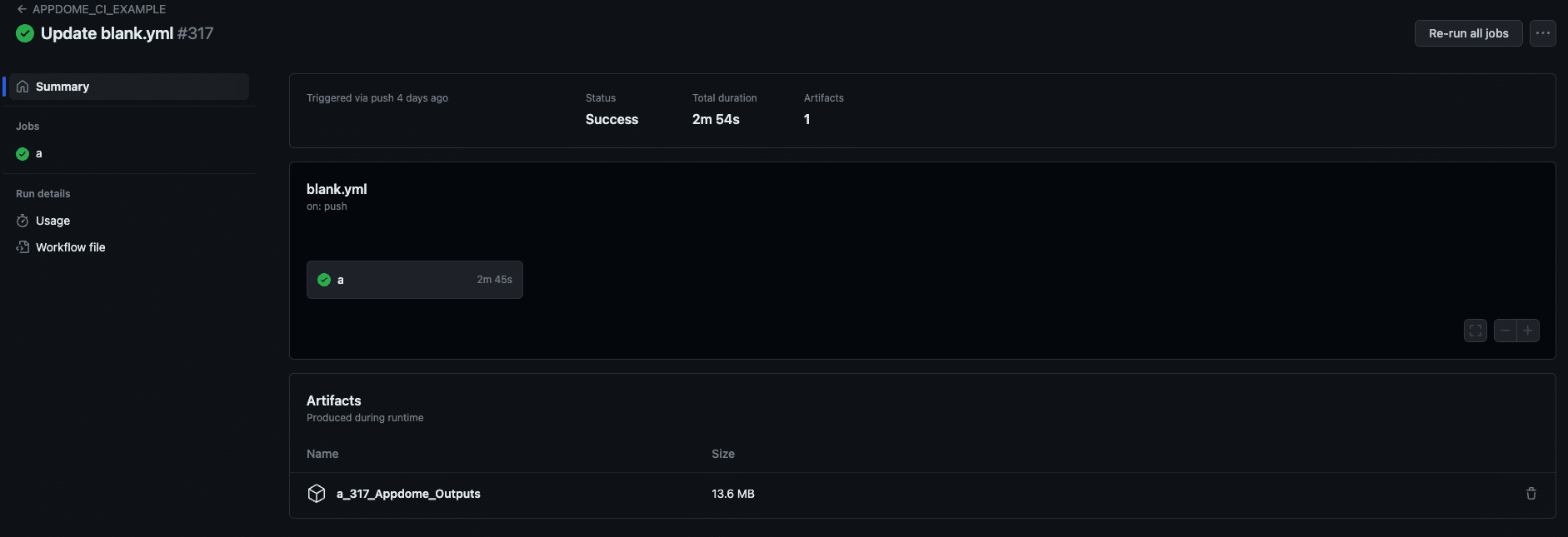
The plugin also exports an artifact with all of Appdome’s output files. The job name and run number determine the artifact’s name.
${{ github.job }}_${{ github.run_number }}_Appdome_Outputs
Every time the workflow runs, the artifact will have a unique name based on the job name and run number, e.g., “My_Job_3_Appdome_Outputs.”
For example, in the following example, the job name is “a,” and the job has been run 317 times.
This guide provides instructions for using the Appdome action to secure and customize mobile apps on GitHub. Following the steps outlined above allows you to automate the process of adding security features to your mobile apps, as well as signing your app with your own enterprise certificate. The Appdome action provides the flexibility and control required to ensure that your mobile apps are secure and customized to meet your specific needs.
Snippet and Action Inputs
The following snippet contains all the necessary action inputs for configuring your workflow. Depending on your specific setup, some of these inputs may not be relevant.
- Appendix A: Appdome Build-2Secure Inputs.
- Appendix B: Sign on Appdome – for Android and iOS.
- Appendix C: Private Signing – for Android and iOS.
- Appendix D: Auto Dev Signing – for Android and iOS.
Be sure to review the relevant appendix to determine which signing option and inputs are required for your pipeline configuration.
Appendix A: Appdome Build-2Secure Inputs
Dynamic Certificates
Certificate pinning is a security technique that is used to ensure that only a specific, trusted server certificate is accepted when establishing HTTPS connections. This prevents attackers from using forged certificates to intercept data and perform man-in-the-middle (MitM) attacks.
DYNAMIC_CERTIFICATES is used for pinning a certificate file to a hostname in the Secure Communication toggle > Certificate Pinning.
The input is a zip file containing the certificate files (e.g., cer, .crt, .zip, .pem, .der), and a JSON file pinning the host to the certificate ({“<host>”: “<cert_file_name>”})
Android Only: Firebase Crashlytics Integration
In addition to securing and signing Android apps, Appdome provides a convenient integration with Firebase Crashlytics to automate the deobfuscation process. With this integration, Appdome can upload deobfuscated mapping files directly to your Crashlytics account.
To enable this, add the following input to your workflow file: FIREBASE_APP_ID
# -Mandatory inputs
APPDOME_API_TOKEN: # Appdome
API KEY: ${{secrets.APPDOME_API_KEY}}
APP_FILE: # none_protected_application can be passed as path/on/repository
# OR https://download_link
FUSION_SET_ID: # Appdome Fusion Set_Id Android/iOS
SIGN_OPTIONS: # “SIGN_ON_APPDOME” OR “PRIVATE_SIGNING” OR “AUTO_DEV_SIGNING”
TEAM_ID: <Your_appdome_team_id>. # Optional
# -Optional input: Dynamic Certificate Pinning
DYNAMIC_CERTIFICATES: ${{secrets.DYNAMIC_CERTIFICATES_ZIP_BASE64}}
# OR path/on/repository/dynamic_certificates.zip
# OR https://download_link
# -Optional inputs, depends on: "SIGN_OPTIONS", Android/iOS #
KEYSTORE_FILE: ${{secrets.KEYSTORE_BASE64}} # Sign keystore file
# OR path/on/repository ...
# OR https://download_link ...
MOBILE_PROVISION_PROFILE_FILE: ${{secrets.PROVISION_PROFILE_BASE64}} ...
# OR <path/on/repository>,<path/on/repository> ...
# OR <https://download_link>,<https://download_link>
ENTITLEMENTS_FILE: ${{secrets.ENTITLEMENTS_BASE64}}
# OR <path/on/repository>,<path/on/repository> ...
# OR <https://download_link>,<https://download_link> ...
# -Optional inputs, general.
SECOND_OUTPUT: true # Adding this will generate a universal .apk file, in addition to the secure .aab app file.
# Note: not supported for Auto-Dev signed apps
BUILD_WITH_LOGS: true # Add to build your app with diagnostic logs.
FIREBASE_APP_ID: "Enter the App ID used in your Firebase project (required for Crashlytics)"
BUILD_TO_TEST:"bitbar"|"browserstack"|"lambdatest"|"saucelabs"| "aws_device_farm" | "perfecto" |"tosca"|"firebase"|"kobiton"|"katalon"
# Specify your selected automated testing service to build the app in test-ready mode.
# Note: in iOS, only saucelabs is supported.
OUTPUT_APP_NAME: output_file_name [no extension]-Optional. This will set the output name for your secured app[will also affect the second output for universal apk's from .aab apps].
Appendix B: SIGN_ON_APPDOME –Android and iOS
Android
For additional information, please refer to the article: Automatic Code Signing for Secured Android Apps on Appdome
APP_FILE: "path/on/repository" OR “https download link”
FUSION_SET_ID: "Appdome fusion set Android"
SIGN_OPTIONS: "SIGN_ON_APPDOME"
APPDOME_API_TOKEN: ${{secrets.APPDOME_API_KEY}}
KEYSTORE_FILE: ${{secrets.KEYSTORE_BASE64}}
KEYSTORE_PASSWORD: ${{secrets.KEYSTORE_PASSWORD}}
KEYSTORE_ALIAS: ${{secrets.KEYSTORE_ALIAS}}
KEYSTORE_KEY_PASSWORD: ${{secrets.KEYSTORE_KEY_PASS}}
iOS
For additional information, please refer to the article: How Appdome Enables Signing Secured iOS Apps without Xcode
Note: When adding multiple entitlements or provisioning profiles, make sure to write them in a single string, with a comma separating them.
APP_FILE: "path/on/repository" OR “https download link”
FUSION_SET_ID: "Appdome fusion set iOS"
SIGN_OPTIONS: "SIGN_ON_APPDOME"
APPDOME_API_TOKEN:${{secrets.APPDOME_API_KEY}}
CERTIFICATE_FILE: ${{secrets.CERTIFICATE_BASE64}}
OR "path/on/repository"
CERTIFICATE_PASSWORD: ${{secrets.CERTIFICATE_PASSWORD}}
ENTITLEMENTS_FILE: "<path/on/repository>,<path/on/repository>" ...
OR “<https_download_link>,<https_download_link>” ....
OR ${{secrets.ENTITLEMENTS_BASE64}}
MOBILE_PROVISION_PROFILE_FILE: "<path/on/repository>,<path/on/repository>" ...
OR "<https_download_link>,<https download link>" ....
OR ${{secrets.PROVISION_PROFILE_BASE64}}
Appendix C: Private Signing – Android and iOS
Android
For additional information, please refer to the article: How to Sign Secured Android Apps Using apksigner
APP_FILE: "path/on/repository" OR “https download link”
FUSION_SET_ID: "Appdome fusion set Android"
SIGN_OPTIONS: "PRIVATE_SIGNING"
APPDOME_API_TOKEN: ${{secrets.APPDOME_API_KEY}}
SIGN_FINGERPRINT: ${{secrets.APPDOME_SIGN_FINGERPRINT}}
GOOGLE_PLAY_SIGNING: "true" -Optional
iOS
For additional information, please refer to the article: How to Sign Secured iOS Apps Using Codesign
Note: When adding multiple entitlements or provisioning profiles, make sure to write them in a single string, with a comma separating them.
APP_FILE: "path/on/repository" OR “https download link”
FUSION_SET_ID: "Appdome fusion set iOS"
SIGN_OPTIONS: "PRIVATE_SIGNING"
APPDOME_API_TOKEN: ${{secrets.APPDOME_API_KEY}}
MOBILE_PROVISION_PROFILE_FILE: "<path/on/repository>,<path/on/repository>" ...
OR “<https_download_link>,<https_download_link>” ....
OR ${{secrets.PROVISION_PROFILE_BASE64}}Appendix D: Auto Dev Signing – ANDROID and iOS
Android
For additional information, please refer to the article: How to Sign Secured Android Apps Using a Local Appdome Supplied Script
APP_FILE: "path/on/repository" OR “https download link”
FUSION_SET_ID: "Appdome fusion set"
SIGN_OPTIONS: "AUTO_DEV_SIGNING"
APPDOME_API_TOKEN: ${{secrets.APPDOME_API_KEY}}
SIGN_FINGERPRINT: ${{secrets.APPDOME_SIGN_FINGERPRINT}}
GOOGLE_PLAY_SIGNING: "true" -OptionaliOS
For additional information, please refer to the article: How to Sign Secured iOS Apps Using a Local Appdome Supplied Script
Note: When adding multiple entitlements or provisioning profiles, make sure to write them in a single string, with a comma separating them.
APP_FILE: "path/on/repository" OR “https download link”
FUSION_SET_ID: "Appdome fusion set iOS"
sign_options: "AUTO_DEV_SIGNING"
APPDOME_API_TOKEN: ${{secrets.APPDOME_API_KEY}}
MOBILE_PROVISION_PROFILE_FILE: "<path/on/repository>,<path/on/repository>" ...
OR “<https_download_link>,<https_download_link>” ....
OR ${{secrets.PROVISION_PROFILE_BASE64}}
ENTITLEMENTS_FILE: "<path/on/repository>,<path/on/repository>" ...
OR “<https_download_link>,<https_download_link>” ....
OR ${{secrets.ENTITLEMENTS_BASE64}}Related Articles:
- How to Secure Android & iOS Apps in Jenkins CI/CD pipelines
- How to Secure Android & iOS Apps in GitLab CI/CD Pipelines
- How to Secure Android & iOS Apps in Bitrise CI/CD Pipelines
How Do I Learn More?
If you have any questions, please send them our way at support.appdome.com or via the chat window on the Appdome platform.
Thank you!
Thanks for visiting Appdome! Our mission is to secure every app on the planet by making mobile app security easy. We hope we’re living up to the mission with your project.
