How to Optimize File Size when Obfuscating Android Apps
This Knowledge Base article describes how to use Appdome’s AI/ML in your CI/CD pipeline to continuously deliver plugins that Prevent obfuscation of publicly available components in Android apps.
Why Prevent Obfuscation of Publicly Available Components?
Obfuscation reduces the efficiency of compression algorithms; therefore, obfuscating all the code in the app may significantly increase its file size. On the other hand, excluding publicly available elements from obfuscation decreases the size of the built app.
Which Libraries are Excluded from Obfuscation?
If you enable Favor App Size, the following libraries will remain deobfuscated:
Open Source Libraries:
| Libraries | Comment |
| libstlport_shared.so | https://developer.android.com/ndk/guides/cpp-support |
| libiconv.so, libzbarjni.so | https://github.com/dm77/ZBarScanner |
| libtool-checker.so | https://github.com/scottyab/rootbeer |
| libcrashlytics.so, libcrashlytics-envelope.so | https://try.crashlytics.com/sdk-android |
| libfirebase.so | https://github.com/firebase/firebase-android-sdk |
| libmpdf.so | https://github.com/mpdf/mpdf |
| libj2v8.so | https://github.com/eclipsesource/J2V8 |
| libjniPdfium.so, libmodpdfium.so | https://pdfium.googlesource.com/pdfium |
| libopencv_imgproc.so, libopencv_core.so, libopencv_java3.so | https://opencv.org |
Xamarin Libraries
libmonodroid.so, libmono-btls-shared.so, libmonosgen-2.0.so, libe_sqlite3.so
React Native
libfb.so, libfolly_json.so, libglog.so, libglog_init.so, libgnustl_shared.so, libicu_common.so, libimagepipeline.so, libjsc.so, libprivatedata.so, libreactnativejni.so, libyoga.so. libc++_shared.so
Unity
libunity.so, libil2cpp.so, libcri_ware_unity.so, libgpg.so
Cordova
libxwalkcore.so, libxwalkdummy.so, libsqlcipher.so
IMPORTANT: Some applications which come with anti-tampering might clash with Appdome’s binary code obfuscation. Read this article to learn more about Appdome’s Anti-Tampering functionality.
Prerequisites for Using Appdome's Favor App's Size Plugins:
To use Appdome’s mobile app security build system to Prevent obfuscation of publicly available components , you’ll need:
- Appdome account (create a free Appdome account here)
- A license for Favor App's Size
- Mobile App (.apk or .aab for Android)
- Signing Credentials (see Signing Secure Android apps and Signing Secure iOS apps)
How to Implement Prevent obfuscation of publicly available components in Android Apps Using Appdome
On Appdome, follow these 3 simple steps to create self-defending Android Apps that Prevent obfuscation of publicly available components without an SDK or gateway:
-
Designate the Mobile App to be protected.
-
Upload an app via the Appdome Mobile Defense platform GUI or via Appdome’s DEV-API or CI/CD Plugins.
-
Android Formats: .apk or .aab
-
Favor App's Size is compatible with: Java, JS, C++, C#, Kotlin, Flutter, React Native, Unity, Xamarin, Cordova and other Android apps.
-
-
Select the defense: Favor App's Size.
-
-
Follow the steps in Sections 2.2-2.2.2 of this article to add the Favor App's Size feature to your Fusion Set via the Appdome Console.
-
When you select the Favor App's Size you'll notice that the Fusion Set you created in step 2.1 now bears the icon of the protection category that contains Favor App's Size.
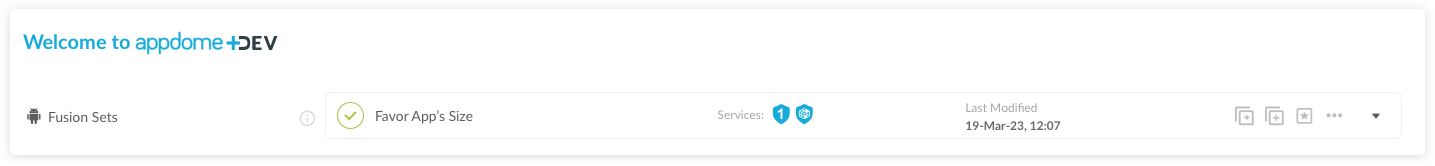
Figure 2: Fusion Set that displays the newly added Favor App's Size protection
Note: Annotating the Fusion Set to identify the protection(s) selected is optional only (not mandatory). -
Open the Fusion Set Detail Summary by clicking the “...” symbol on the far-right corner of the Fusion Set. Copy the Fusion Set ID from the Fusion Set Detail Summary (as shown below):
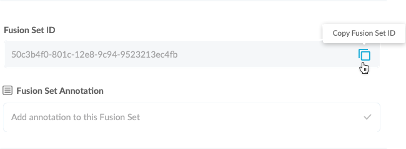
Figure 3: Fusion Set Detail Summary
-
Follow the instructions below to use the Fusion Set ID inside any standard mobile DevOps or CI/CD toolkit like Bitrise, Jenkins, Travis, Team City, Circle CI or other system:
-
Refer to the Appdome API Reference Guide for API building instructions.
-
Look for sample APIs in Appdome’s GitHub Repository.
-
Create and name the Fusion Set (security template) that will contain the Favor App's Size feature as shown below: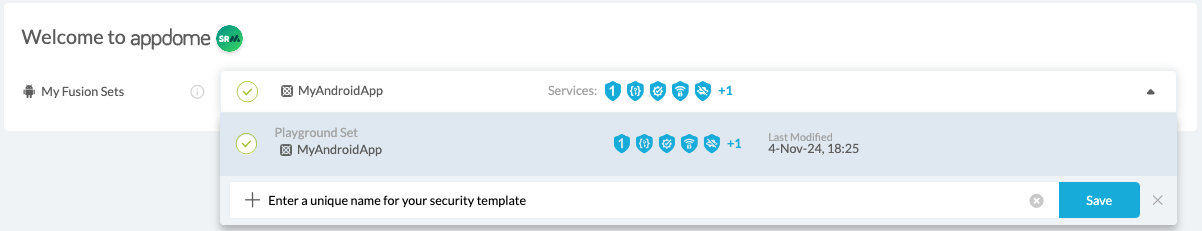
Figure 1: Fusion Set that will contain the Favor App's Size feature
-
-
Add the Favor App's Size feature to your security template.
-
Navigate to Build > Security tab > TOTALCode™ Obfuscation section in the Appdome Console.
-
Toggle On Favor App's Size.

Figure 4: Selecting Prevent obfuscation of publicly available components
-
Congratulations! The Favor App's Size protection is now added to the mobile app -
-
Certify the Favor App's Size feature in Android Apps
After building Favor App's Size, Appdome generates a Certified Secure™ certificate to guarantee that the Favor App's Size protection has been added and is protecting the app. To verify that the Favor App's Size protection has been added to the mobile app, locate the protection in the Certified Secure™ certificate as shown below:

Figure 5: Certified Secure™ certificate
Each Certified Secure™ certificate provides DevOps and DevSecOps organizations the entire workflow summary, audit trail of each build, and proof of protection that Favor App's Size has been added to each Android app. Certified Secure provides instant and in-line DevSecOps compliance certification that Favor App's Size and other mobile app security features are in each build of the mobile app.
Using Appdome, there are no development or coding prerequisites to build secured Android Apps by using Favor App's Size. There is no SDK and no library to code or implement in the app and no gateway to deploy in your network. All protections are built into each app and the resulting app is self-defending and self-protecting.
Releasing and Publishing Mobile Apps with Favor App's Size
After successfully securing your app by using Appdome, there are several available options to complete your project, depending on your app lifecycle or workflow. These include:
- Customizing, Configuring & Branding Secure Mobile Apps.
- Deploying/Publishing Secure mobile apps to Public or Private app stores.
- Releasing Secured Android & iOS Apps built on Appdome.
Related Articles:
- Binary Code Obfuscation, Anti-Reversing for Android & iOS Apps
- How to Encrypt Java Class Files (.dex) in Android Apps
- Dex Control Flow Relocation, Anti-Reversing for Android Apps
- Non-Native Code Obfuscation, Anti-Reversing for Android & iOS Frameworks
How Do I Learn More?
If you have any questions, please send them our way at support.appdome.com or via the chat window on the Appdome platform.
Thank you!
Thanks for visiting Appdome! Our mission is to secure every app on the planet by making mobile app security easy. We hope we’re living up to the mission with your project.
